Learn how Vulnerability scanning works and how it strengthens your security posture by identifying and addressing potential weaknesses.
Vulnerability scanning is an automated process designed to identify, assess, and report security flaws across devices, networks, and applications. It is a foundational pillar of modern cybersecurity, enabling organizations to find and fix weaknesses before attackers can exploit them.
Without a consistent scanning program, organizations are essentially navigating their IT environment blindfolded. Threats evolve every day, and a single unpatched system or misconfigured service can be the entry point that leads to a costly breach.

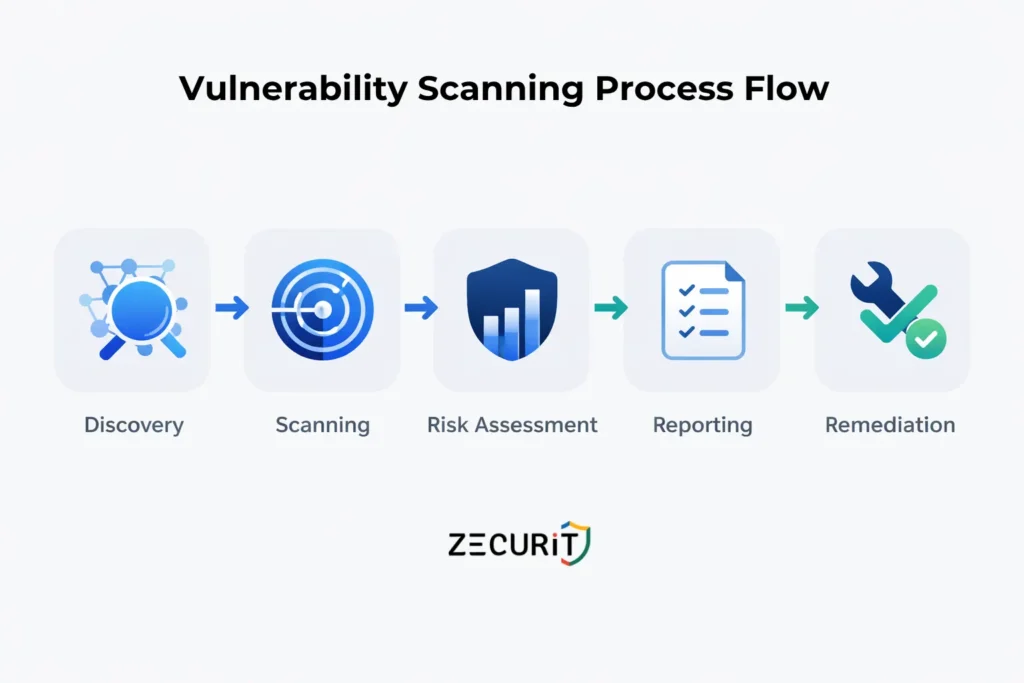
Vulnerability scanning relies on automated tools that examine a system's network, software, and configurations in a structured sequence. Here is how the process typically unfolds:
The scanner begins by identifying all systems, devices, and software connected to the network. This network discovery phase creates a comprehensive map of the entire IT infrastructure, ensuring nothing is missed before the actual scan begins. This step is closely related to broader endpoint management practices that maintain visibility across all connected assets.
Once assets are discovered, the scanner examines each one for known vulnerabilities. It cross-references findings against a continuously updated vulnerability database such as the Common Vulnerabilities and Exposures (CVE) list, maintained by MITRE. Weaknesses it looks for include outdated software, insecure configurations, open ports, and weak passwords.
Not every vulnerability is equal. After detection, the scanner evaluates each finding based on factors such as exploitability, potential impact, and exposure level. Vulnerabilities are typically categorized as low, medium, high, or critical, helping security teams prioritize their response. This kind of risk-based thinking is central to a strong security posture.
The scanner generates a detailed report that outlines identified vulnerabilities, their severity ratings, and remediation recommendations. These reports typically include suggested patches, configuration changes, and other corrective measures.
After the report is delivered, security teams act on the findings. This may involve applying patches, adjusting firewall rules, enforcing stronger passwords, or reconfiguring services. A follow-up scan is always recommended to verify that the remediation was effective. This connects directly to a mature patch management workflow.
Vulnerability scanning is not optional for organizations serious about security. Here is why it matters:
Early Detection of Threats Scanning allows security teams to find and resolve weaknesses before attackers do. A proactive approach significantly reduces the risk of data breaches, system outages, and compromised credentials. Learn more about top cybersecurity vulnerabilities that scanning can help uncover.
Regulatory Compliance Many industries require regular vulnerability assessments to comply with cybersecurity regulations including PCI-DSS, HIPAA, GDPR, and NIST. Failing to adhere to these standards can result in significant fines and legal exposure.
Reducing the Attack Surface Every unaddressed vulnerability is a potential doorway for attackers. By systematically identifying and fixing weaknesses, organizations shrink the attack surface, making it significantly harder for threats to gain a foothold. This is a key goal of endpoint security.
Improving Incident Response Consistent scanning keeps security teams informed about the current risk landscape. This awareness enables faster and more effective responses when new threats emerge, feeding directly into a stronger overall vulnerability management program.
Cost-Effective Security Identifying and remediating a vulnerability before it is exploited is far less expensive than dealing with the aftermath of a breach, including legal fees, regulatory penalties, and reputational damage. Regular scanning is one of the most cost-efficient investments in cybersecurity best practices.
Different environments require different scanning approaches. Here are the most common types:
This scan focuses on the network infrastructure, including routers, switches, firewalls, and servers. It checks for weaknesses such as open ports, insecure protocols, and misconfigurations that could allow unauthorized access.
Common tools: Nessus, OpenVAS, Qualys, Nexpose

Web application scanners detect flaws specific to web-based software, including SQL injection, Cross-Site Scripting (XSS), and broken authentication. Given how frequently web apps are targeted, this type of scanning is critical for any organization with an online presence. It pairs well with a broader security audit process.
Common tools: OWASP ZAP, Burp Suite, Acunetix, Netsparker
Host-based scanning targets individual systems such as servers and workstations. It examines operating systems, installed applications, and configurations for known vulnerabilities. It can also detect unauthorized software, malware, and weak account credentials.
Common tools: Retina, Qualys, Rapid7 Nexpose
Databases store the most sensitive organizational data, making them high-value targets. This scan type looks for misconfigurations, outdated database versions, missing patches, and other weaknesses that could expose sensitive records.
Common tools: IBM AppScan, DBProtect, Oracle Database Vault
As organizations shift workloads to the cloud, dedicated cloud scanning has become essential. It identifies misconfigurations, insecure access controls, and risks specific to cloud infrastructure and services, helping ensure both the provider's and the customer's security controls meet expectations.
Common tools: CloudPassage, Prisma Cloud, Dome9, Tenable.io
Wireless networks are a common vector for unauthorized access and eavesdropping. This scan type uncovers weaknesses in Wi-Fi configurations, including open ports, weak encryption, and insecure setups.
Common tools: Aircrack-ng, Kismet, Nessus
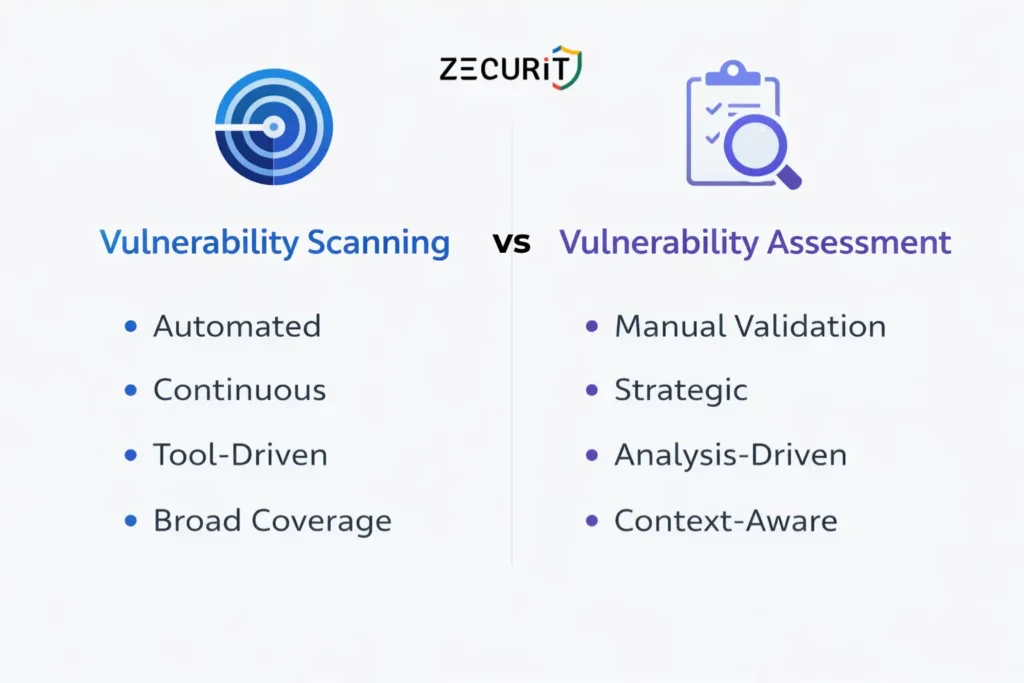
These two terms are often used interchangeably, but they are not the same thing.
Vulnerability scanning is an automated, repeatable process. It produces a list of detected weaknesses based on known signatures and patterns.
Vulnerability assessment is a broader, more analytical process. It includes scanning but also involves manual validation, contextual risk analysis, and strategic prioritization. Think of scanning as a component within a full vulnerability assessment program.
Understanding the distinction helps organizations allocate resources appropriately and build a more complete security program.
For organizations committed to a strong cybersecurity posture, regular vulnerability scanning delivers measurable returns:
To get maximum value from a scanning program, organizations should follow these guidelines:
Scan Regularly New vulnerabilities are discovered every day. Establish a consistent scanning schedule, whether weekly, monthly, or triggered by significant changes in the environment. Staying current with Patch Tuesday updates is a good baseline for understanding the latest software vulnerabilities from major vendors.
Ensure Comprehensive Coverage Scan everything: internal systems, external-facing applications, cloud workloads, and network devices. Gaps in coverage create blind spots that attackers will find before you do.
Prioritize Critical Vulnerabilities After each scan, focus remediation efforts on critical and high-severity findings first. Use CVSS scores and contextual risk factors to make informed prioritization decisions.
Pair Scanning with Patch Management Vulnerability scanning is most effective when integrated with a disciplined patch management workflow. Discovered vulnerabilities should trigger a defined remediation and patching process, not just a report.
Use Multiple Scanning Tools No single scanner covers every environment perfectly. Combining tools, for example using one for network scanning and another for web application scanning, results in broader and more accurate coverage.
Track and Report Findings Over Time Maintain a vulnerability register and track remediation progress over time. Trend data helps demonstrate improvement to stakeholders and supports compliance reporting.
Implement Zero Trust Principles Zero trust security complements vulnerability scanning by ensuring that even if a vulnerability exists, lateral movement within the environment is restricted by default.
Understanding the limitations of scanning helps organizations use it more effectively:
False Positives Scanners can flag issues that are not actually exploitable in a given environment. Security teams need to validate findings and tune scanner configurations over time to reduce noise.
Scan Frequency vs. Business Impact Aggressive scanning can impact system performance. Scheduling scans during maintenance windows and using agent-based scanning where possible helps minimize disruption.
Scope Creep and Asset Discovery Gaps Shadow IT and undiscovered assets are a persistent problem. Organizations should invest in continuous asset discovery alongside vulnerability scanning to ensure complete coverage.
Credential Management Authenticated scanning, which logs into systems using credentials, produces far more accurate results than unauthenticated scanning. Managing credentials securely for this purpose is an operational challenge worth solving.
Vulnerability scanning is a non-negotiable element of any mature cybersecurity program. It gives organizations a clear, ongoing picture of their security weaknesses, enabling them to act before attackers do. By combining regular scans with disciplined remediation, robust patch management, and a broader vulnerability management strategy, organizations can substantially reduce their risk exposure and build lasting resilience.
Whether you are just starting to formalize your security processes or looking to optimize an existing program, vulnerability scanning is where proactive security begins.
Vulnerability scanning is an automated process that identifies, evaluates, and reports security weaknesses in systems, networks, and applications to prevent exploitation.
It helps detect and fix vulnerabilities before they can be exploited by attackers, reducing the risk of breaches, data loss, and ensuring compliance with regulations.
Common types include network vulnerability scanning, web application scanning, host-based scanning, cloud vulnerability scanning, and database vulnerability scanning.
Vulnerability scanning should be done regularly, at least quarterly, or after major system updates, patches, or when new vulnerabilities are discovered.
Vulnerabilities are prioritized based on their severity, exploitability, and potential impact. Critical vulnerabilities should be addressed immediately, followed by high-risk ones.