A complete guide to identifying, tracking, and maintaining visibility across IT assets!
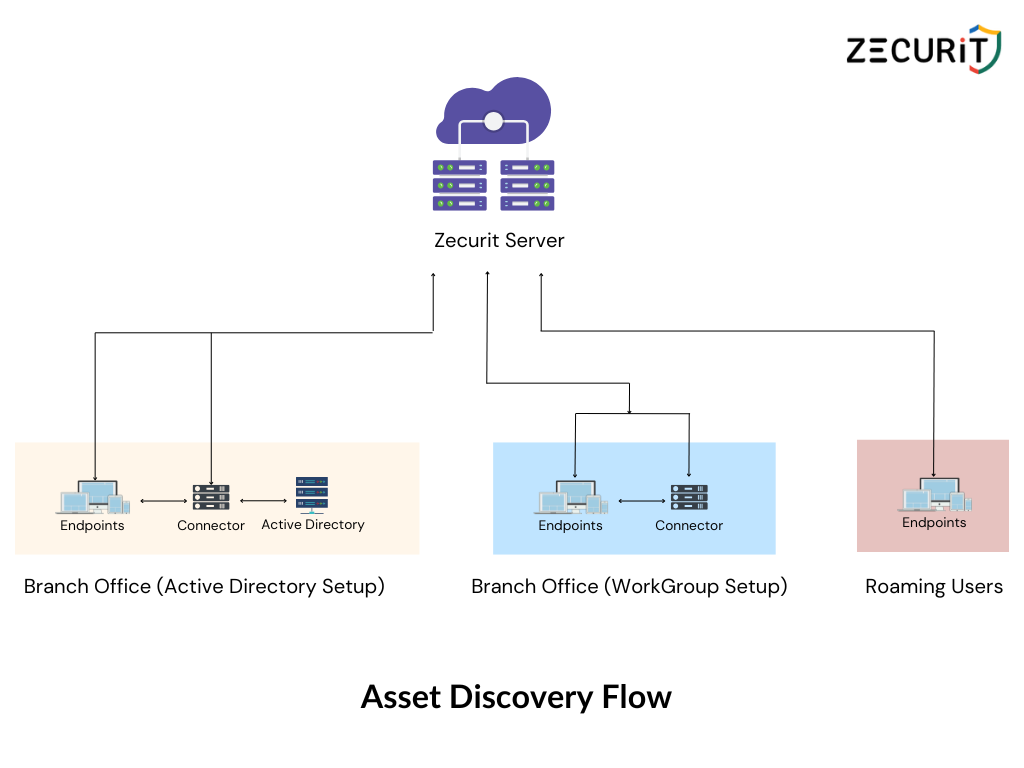
Modern IT environments are no longer confined to a single office or data center. Organizations today manage a mix of endpoints, servers, cloud infrastructure, and SaaS applications—often spread across locations and teams. In this context, maintaining an accurate view of what assets exist is both difficult and essential.
IT asset discovery is the process that makes this visibility possible. It ensures organizations know what assets they have, where they are, and how they are being used, forming the foundation of effective IT Asset Management (ITAM).
IT asset discovery is the systematic process of identifying, collecting, and maintaining information about all IT assets within an organization. These assets typically include:
Unlike manual inventories or spreadsheets, asset discovery is designed to be automated and continuous, allowing asset data to remain accurate as environments change.
ITAM relies on accurate data. Without reliable discovery, asset records quickly become outdated, leading to inefficiencies and risk.
Effective asset discovery helps organizations:
In short, asset discovery provides the source of truth that all ITAM activities depend on.
Different environments require different discovery approaches. Most organizations use a combination of methods to achieve full coverage.
Network-based discovery scans the network to identify connected devices such as servers, workstations, routers, switches, and printers.
This method is useful for gaining a quick, high-level view of on-premise assets but may lack detailed configuration data.
Agent-based discovery involves deploying lightweight software agents on endpoints. These agents collect detailed information about:
This approach provides deep and continuous visibility, making it well suited for environments that require precise asset data.
Agentless discovery collects asset information without installing software agents, using standard protocols such as SNMP, WMI, or SSH.
It is commonly used for network devices, servers, or systems where agent installation is not feasible.
As infrastructure shifts to cloud and SaaS platforms, traditional discovery methods alone are no longer sufficient.
Cloud and SaaS discovery focuses on identifying:
This type of discovery is essential for maintaining visibility in hybrid and cloud-first environments.
Despite being foundational to IT Asset Management, asset discovery is often where ITAM programs start to break down. The most common challenges are not technical alone—they are operational and organizational.
Modern IT stacks span on-premise infrastructure, multiple cloud providers, SaaS tools, and remote endpoints. No single discovery method covers all of these environments equally well, leading to partial visibility and data silos.
Employees increasingly adopt SaaS tools without IT involvement. These applications often bypass traditional discovery mechanisms, making it difficult to track usage, ownership, data access, and compliance risk.
One-time or infrequent scans quickly become outdated in dynamic environments. Assets are provisioned, reassigned, or retired constantly, causing inventories to drift from reality if discovery is not continuous.
Discovery tools may identify devices or applications but fail to capture contextual information such as asset ownership, business criticality, or lifecycle stage—limiting the usefulness of the data for ITAM decisions.
Agent-based approaches can introduce deployment, maintenance, and versioning challenges, especially at scale. Conversely, agentless methods may struggle with depth or access limitations.
Incomplete discovery leads to gaps during audits. Missing or undocumented assets can create compliance risks, particularly for frameworks such as SOC 2, ISO 27001, or HIPAA.
Mature ITAM programs treat asset discovery as a continuous discipline, not a setup task. The following best practices reflect how experienced IT teams maintain accurate visibility over time.
One-time or quarterly scans are insufficient in modern IT environments. Continuous or frequent discovery ensures asset records reflect real-world changes such as device reassignment, software installs, or cloud provisioning.
Relying on a single method often results in blind spots. Combining agent-based, agentless, network-based, and cloud integrations provides broader and more reliable coverage across environments.
Asset data should feed into a centralized inventory or CMDB where it can be normalized, deduplicated, and enriched. Fragmented asset data reduces trust and limits downstream ITAM effectiveness.
Discovery should go beyond identifying what exists. Mapping assets to Owners or departments, Business criticality, Lifecycle stage, Compliance requirements turns raw discovery data into actionable ITAM intelligence.
Discovered assets should be continuously compared against existing records to identify:
Reconciliation is critical to maintaining data accuracy over time.
SaaS applications and cloud resources should be treated as first-class assets, not add-ons. Early inclusion reduces shadow IT, improves spend visibility, and supports security governance.
Asset discovery data is valuable beyond ITAM. Sharing discovery outputs with security and compliance teams improves vulnerability management, access reviews, and audit preparedness.
Zecurit’s ITAM capabilities are designed to support continuous, accurate asset visibility across modern IT environments. Rather than relying on one-time scans or manual updates, Zecurit enables IT teams to maintain an up-to-date view of hardware and software assets with minimal operational overhead.
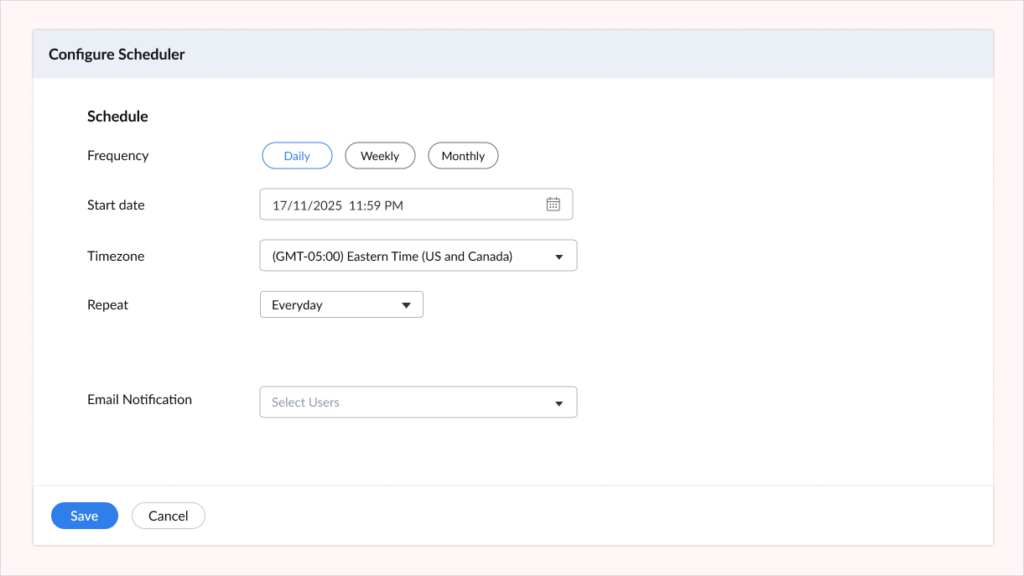
Automate asset scans to effortlessly discover and inventory all IT assets at scheduled times
Zecurit allows IT teams to configure automated, scheduled discovery scans across managed endpoints, including desktops, laptops, and servers. These scans run at predefined intervals and collect detailed hardware and software attributes from each endpoint.
The discovered data is automatically synchronized with Zecurit’s central asset repository, ensuring asset records remain current as devices are added, updated, or reassigned.
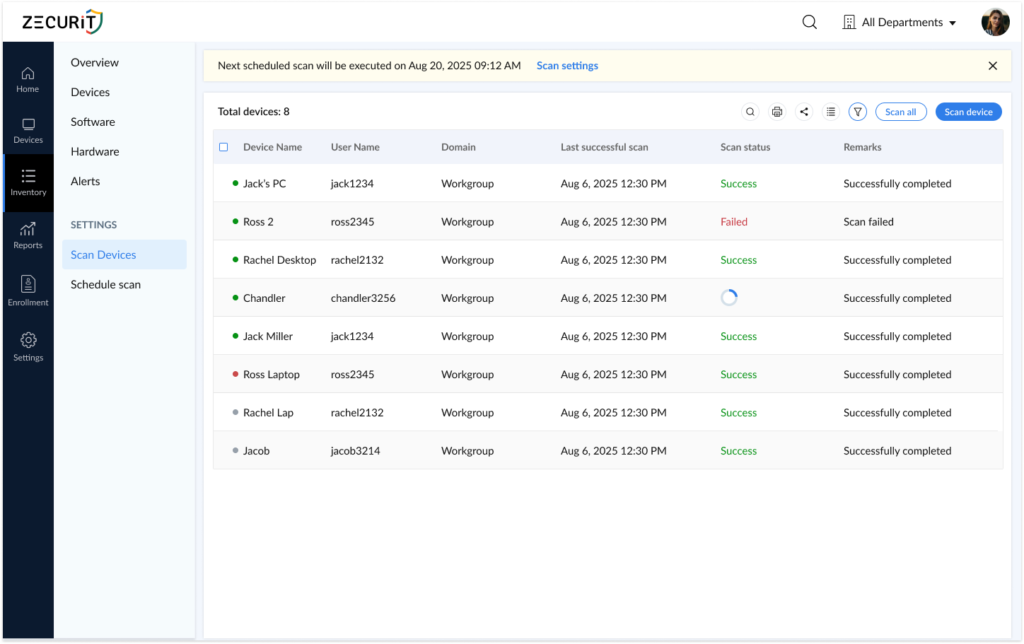
Instantly scan and detect all IT assets with our On Demand Inventory Scan feature, ensuring up-to-date visibility and comprehensive control.
Zecurit also supports on-demand asset scans, enabling immediate discovery of selected devices or asset groups. This is particularly useful in scenarios such as security investigations, audit preparation, or operational troubleshooting where real-time asset data is required.
On-demand scans provide up-to-date visibility without waiting for the next scheduled discovery cycle.
To support targeted use cases, Zecurit offers custom scan configurations that allow IT teams to collect only specific data points instead of performing a full inventory scan. For example, teams can retrieve installed software details, configuration attributes, or compliance-related information as needed.
This approach helps reduce unnecessary data collection while still supporting precise ITAM and audit workflows.
Organizations use Zecurit to establish a reliable asset discovery foundation without the manual effort typically associated with maintaining IT inventories. By centralizing discovery data and keeping asset records continuously updated, Zecurit enables IT teams to:
Zecurit’s asset discovery capabilities integrate directly into broader IT Asset Management workflows, ensuring that discovery data remains actionable rather than static.
Gain real-time visibility into all your IT assets, automate network scans and ensure your organization’s security and compliance.
Zecurit can discover and track a wide range of assets, including hardware (servers, desktops, laptops) and software (operating systems, applications and versions).
No, Zecurit is designed to conduct scans with minimal effect on network performance. You can schedule scans during non-office hours or adjust the scan settings for added flexibility.
Yes. Zecurit's solution offers a "Schedule Scanning" feature that allows you to automate inventory scans across your environment for all managed endpoints. You can also perform on-demand or custom scans whenever needed.
The central goal of asset discovery is to build a comprehensive, up-to-the-minute inventory of all your organization's IT assets, both hardware and software. This foundational process is the essential first step for any effective IT asset management (ITAM) strategy, ensuring you have a clear, real-time view of every asset in your environment.
The frequency depends on how dynamic the environment is. In most modern IT environments, continuous or daily discovery is recommended to prevent data drift. On-demand scans are typically used for audits, security incidents, or operational checks.
Yes. Modern asset discovery extends beyond physical devices to include cloud infrastructure, virtual machines, and SaaS applications. This is especially important for identifying shadow IT and maintaining visibility in hybrid or cloud-first environments.
Asset discovery significantly reduces the need for manual tracking by automating data collection. However, manual input may still be required to add business context such as ownership, cost centers, or usage policies.
Zecurit uses scheduled and on-demand discovery scans to continuously refresh asset data. This ensures changes such as new devices, software updates, or asset reassignments are reflected without manual intervention.
Asset discovery provides an accurate and verifiable record of assets, which is critical for audits and compliance frameworks such as ISO 27001 or SOC 2. Complete discovery reduces the risk of missing or undocumented assets during assessments.
Disover the essential features and functionalities of Zecurit Asset Manager.
Automatically discover all IT assets across your network for complete inventory visibility.
Track all software installations and ensure accurate license utilization to avoid costly audits.
Track all hardware assets, from desktops to servers, for effective monitoring and proactive maintenance.
Manage software licenses effectively, reduce costs, and ensure compliance with vendor agreements.
Monitor software usage in real-time to optimize license utilization and maximize your software investments.
Generate insightful reports on asset utilization, software usage and other key metrics to make informed decisions.