Every 60 seconds, your organization is leaking money through unmanaged IT assets. While you're reading this sentence, unused software licenses are draining your budget, unpatched devices are creating security vulnerabilities and ghost assets are multiplying in the shadows of your infrastructure.
The reality is stark: Organizations without formal IT Asset Management (ITAM) waste an average of 30% of their software spend annually, that's $15 million for a company with a $50 million IT budget. According to IBM's 2025 Cost of a Data Breach Report, the average breach now costs $4.88 million, with unpatched and unmanaged devices serving as the primary entry point in 43% of incidents.
If you're a CFO, CIO or procurement director who views ITAM as a "nice-to-have" expense rather than a strategic imperative, this article presents the business case you need. The question isn't whether you can afford ITAM, it's whether you can afford another day without it.
SaaS sprawl has become the silent profit killer in modern enterprises. Gartner's 2025 IT Asset Management Market Guide reveals that organizations waste between $1,000 to $2,500 per employee annually on unused or underutilized software licenses. For a 500-person company, that's up to $1.25 million evaporating each year.
Without ITAM, your organization likely has no visibility into who's actually using what. Marketing purchased 50 Adobe Creative Cloud licenses two years ago, but only 18 employees actively use them. Engineering subscribed to three different project management tools, with teams scattered across platforms. Finance approved a Salesforce expansion that went 40% unutilized.
Ghost assets are devices, licenses or equipment that exist in your procurement records but have vanished from operational visibility. They're laptops sitting in former employees' homes, monitors in storage closets and software licenses assigned to accounts that no longer exist.
The true cost of a ghost asset extends beyond the initial purchase price. Consider a $2,000 laptop that becomes a ghost asset. You're also paying for:
The software licenses assigned to it ($500-$1,500 annually)
Continued security management attempts ($200 annually)
The opportunity cost of not reallocating it to a productive user ($3,000+ in delayed productivity)
Compliance risk if it contains sensitive data (potentially millions in breach costs)
For a mid-sized enterprise with 1,000 endpoints, even a conservative 10% ghost asset rate translates to $420,000 in annual waste on hardware alone, before adding software licensing costs.
Your organization likely has a spending problem if you're experiencing:
Multiple subscriptions to overlapping tools. Teams independently purchasing Slack, Microsoft Teams, Zoom and Google Meet demonstrates zero coordination and 300% redundancy.
No automated process for license reclamation. When employees leave, their licenses should be immediately reassigned. Without ITAM, they sit dormant for an average of 147 days.
Reactive hardware procurement. You're ordering new devices on a crisis basis rather than following a strategic refresh cycle, paying premium prices for rush orders.
Shadow IT exceeding 40% of total applications. Flexera's 2025 State of ITAM Report found that organizations without formal asset management have shadow IT rates exceeding 40%, compared to just 12% for ITAM-mature organizations.
Finance and IT speaking different languages. Your CFO can't connect software spend to business outcomes and your IT team can't explain TCO to the board.
Total Cost of Ownership (TCO) encompasses far more than sticker prices. Without ITAM organizations systematically underestimate TCO by 35-50% because they're not tracking:
Deployment costs and time-to-productivity delays
Ongoing maintenance, support and upgrade expenses
Integration costs with existing systems
Training requirements and learning curve inefficiencies
End-of-life disposal and data sanitization costs
Opportunity costs from suboptimal asset utilization
A $1,500 laptop doesn't cost $1,500. Over its 3-year lifecycle, the true TCO ranges from $5,000 to $8,000 when you include support, software, security and management overhead. Organizations without ITAM make procurement decisions based on incomplete financial data, consistently choosing options that appear cheaper upfront but cost more over time.
Cybercriminals don't need sophisticated zero-day exploits when your infrastructure is riddled with unpatched vulnerabilities. The 2025 Verizon Data Breach Investigations Report confirms that 76% of network intrusions exploited known vulnerabilities with patches available for more than 90 days.
Without ITAM, you don't know what devices exist, where they are or their patch status. That laptop your former sales director took home eight months ago? It's still connected to your VPN with vulnerabilities from 2023. The test server your developers spun up last quarter? It's running an outdated OS version that's become a ransomware target.
Organizations with comprehensive ITAM practices experience data breaches that cost $1.76 million less on average than those without, according to IBM's latest research. The difference comes from faster detection, contained scope and reduced recovery time.
Consider what attackers gain from unmanaged IT assets:
Lateral movement opportunities. Unknown devices provide unmonitored pathways through your network, allowing attackers to move from compromised endpoints to critical systems.
Credential harvesting. Ghost assets often retain active credentials that haven't been rotated in months or years, providing easy access points.
Data exfiltration staging. Unmonitored devices serve as temporary storage for stolen data before external transfer, avoiding detection by security tools focused on known assets.
Ransomware deployment platforms. Attackers use unmanaged devices to deploy ransomware across networks because these endpoints lack EDR protection and monitoring.
Shadow IT applications and services used without IT department approval, represents an enterprise security crisis. Employees adopt convenient cloud tools without considering security implications, creating data silos outside your security perimeter.
Without ITAM's discovery and monitoring capabilities, shadow IT flourishes. Employees share sensitive customer data through unapproved file-sharing services, store intellectual property in personal cloud accounts and integrate unsanctioned applications with core business systems.
The average shadow IT security incident costs $4.2 million to remediate, including breach notification, regulatory fines, customer compensation and reputation damage. These incidents occur because organizations lack visibility into what applications are accessing their data and who's authorizing these connections.
Physical hardware poses security risks that extend beyond cyber vulnerabilities. Without accurate inventory tracking:
Lost or stolen devices average 68 days before being reported, providing criminals ample time to extract data or use credentials for network access.
Improperly disposed equipment containing unwiped drives has appeared in secondary markets with sensitive corporate data intact, leading to GDPR violations costing €20 million in one 2024 case.
Unauthorized device connections to corporate networks go undetected because there's no baseline of authorized hardware to compare against.
Warranty and support lapses leave critical infrastructure without vendor support during security incidents, extending downtime from hours to weeks.
The financial impact compounds when you consider that ransomware attacks specifically targeting organizations with poor asset visibility have increased 156% year-over-year, according to cybersecurity firm Recorded Future's 2025 Threat Landscape Report.
Microsoft oracle, Adobe and IBM don't schedule audits as friendly check-ins. These are revenue-generating exercises where vendors systematically identify licensing gaps and organizations without comprehensive ITAM documentation face penalty assessments averaging $3.8 million according to ITAM Review's 2025 Software Audit Defense Survey.
The audit scenario unfolds predictably for unprepared organizations:
Week 1-2: Vendor issues audit notice requesting complete licensing documentation within 30 days. Your team scrambles to compile spreadsheets from multiple sources.
Week 3-4: You discover critical gaps. That server virtualization project from 2022? Nobody documented the licensing implications. Those developer tools? Three teams purchased seats independently and there's overlap everywhere.
Month 2-3: The vendor's audit team identifies "compliance gaps" totaling 156% of your known licenses. They present a settlement proposal requiring immediate payment plus mandatory purchase commitments for the next three years.
Month 4-6: Legal involvement, negotiation attempts and ultimately payment of penalties plus retroactive licensing fees, typically 60-80% of the vendor's initial claim, but still millions in unbudgeted expenses.
Vendor audit penalties represent only the visible portion of total costs. Organizations also incur:
Internal resource costs: 400-800 hours of senior IT staff time diverted from strategic projects, representing $80,000-$160,000 in fully-loaded labor costs.
External consultant fees: Specialized software audit defense consultants charge $15,000-$50,000 to help navigate complex licensing negotiations.
Opportunity costs: Strategic initiatives delayed by 4-6 months while the team focuses on audit response.
Forced purchasing commitments: Vendors often require 3-year advance purchase commitments as part of settlements, locking organizations into spending regardless of actual needs.
Relationship damage: Post-audit vendor relationships become adversarial, eliminating partnership opportunities and preferential pricing.
Poor IT asset tracking creates regulatory compliance nightmares that result in substantial fines and legal exposure. Under GDPR organizations must demonstrate data processing controls, know where personal data resides and prove data security measures are in place.
Without ITAM, answering basic regulatory questions becomes impossible:
"What devices have access to EU citizen data?" (GDPR Article 30 compliance)
"Can you produce records of all systems processing payment information?" (PCI-DSS requirements)
"What security controls protect devices accessing healthcare data?" (HIPAA compliance)
"Where is our customer data stored and who has accessed it?" (SOC2 audit requirements)
GDPR fines have reached €1.3 billion for data protection violations in 2024, with poor asset visibility cited as a contributing factor in 34% of cases. Organizations that couldn't demonstrate knowledge of where personal data resided or what security controls protected it faced maximum penalty tiers.
Organizations without ITAM often maintain what we call "audit readiness theater", the illusion of compliance through outdated spreadsheets, manual inventory efforts and periodic "cleanup" campaigns.
This approach fails catastrophically during actual audits because:
Spreadsheets are outdated within 48 hours of creation in dynamic IT environments.
Manual inventories miss 30-40% of assets according to benchmark studies.
Point-in-time snapshots don't demonstrate continuous compliance required by most regulations.
No audit trail exists to prove historical compliance, only current status.
The false confidence from audit readiness theater actually increases risk by preventing organizations from implementing legitimate solutions. You believe you're compliant until an audit proves otherwise, at which point remediation costs have compounded exponentially.
New employee onboarding should take hours, not days. Yet organizations without ITAM average 8.3 days from hire date to full productivity, compared to 2.1 days for ITAM-mature organizations, according to Aberdeen Group's 2025 IT Service Delivery Benchmarks.
The onboarding delay stems from chaotic asset provisioning:
IT doesn't know what equipment is available for reassignment, so they order new devices with 5-7 day shipping delays.
Software licenses can't be quickly reallocated because nobody knows what's already licensed but unused.
Account provisioning follows manual processes involving multiple teams and approval loops.
Training on tools and systems is delayed because access isn't properly sequenced.
For a 500-person organization with 15% annual turnover, the productivity cost of inefficient onboarding approaches $780,000 annually (75 employees × 6.2 days delay × $210 average daily productivity value).
Equipment failure in organizations without asset management triggers operational chaos. Without tracking warranty status, maintenance history and spare part availability, a simple laptop failure cascades:
Hour 0: Employee laptop fails. Ticket created.
Hour 4: IT determines the device is out of warranty (nobody tracked expiration). Repair will take 5-7 business days.
Day 1: IT searches for spare devices. The "spare laptop" inventory is inaccurate, supposedly available devices are actually deployed or broken.
Day 2: Emergency hardware purchase approved. Expedited shipping adds 40% cost premium.
Day 3-4: New device arrives, requires imaging, software installation and configuration.
Day 5: Employee finally receives working device but has lost 5 days of productivity and missed critical deadlines.
Cost per incident: $4,200 (device cost + premium + lost productivity + IT labor). Organizations without ITAM experience these incidents 3.7x more frequently than those with proper lifecycle planning and spare inventory management.
Strategic IT asset lifecycle planning enables organizations to refresh hardware on optimized schedules, negotiate volume pricing and minimize disruption. Without ITAM-driven lifecycle planning organizations operate in permanent reactive mode:
Crisis-driven purchases command 25-40% price premiums for expedited shipping and rush processing.
No volume discounts because purchases occur sporadically rather than in strategic bulk orders.
Suboptimal refresh timing leads to extended use of inefficient hardware that costs more to maintain than replace.
Technology debt accumulation as aging assets require custom support and compatibility workarounds.
The financial impact is substantial. Organizations with mature ITAM practices reduce their hardware TCO by 23% through strategic lifecycle planning, according to Gartner's 2025 ITAM Best Practices research.
Poor asset management doesn't just affect IT, it cascades through every business function:
Sales teams lose deals because CRM access issues delay quote generation. Cost per lost opportunity: $47,000 average.
Finance teams can't close books on schedule because procurement data is scattered across systems. Cost per delayed close: 120 hours of senior accountant time plus compliance risk.
HR teams can't complete background checks because IT provisioning delays prevent new hires from starting. Cost per delayed start: $840 per day per position unfilled.
Customer support teams experience longer resolution times because they lack proper tools or access. Cost per percentage point of satisfaction decline: $230,000 annually in customer churn for mid-sized B2B organizations.
When you aggregate these operational inefficiencies, the total productivity tax of poor asset management ranges from $2.4 million to $6.7 million annually for organizations with 500-1,500 employees.
Not all ITAM deficiencies carry equal risk. This matrix helps executives prioritize where poor asset management threatens the organization most severely:
Unpatched Security Vulnerabilities on Critical Systems
Risk Level: Critical
Potential Cost: $3.5M - $8.9M (breach costs)
Time to Impact: 30-90 days
Mitigation Priority: Immediate
No Software License Compliance Documentation
Risk Level: Critical
Potential Cost: $1.8M - $5.2M (audit penalties)
Time to Impact: 60-180 days (typical audit notice to resolution)
Mitigation Priority: Immediate
Shadow IT with Access to Regulated Data
Risk Level: High
Potential Cost: $2.1M - $4.8M (regulatory fines + breach costs)
Time to Impact: 90-180 days
Mitigation Priority: 30 days
Poor Hardware Lifecycle Planning
Risk Level: Medium
Potential Cost: $420K - $890K annually (excess procurement + downtime)
Time to Impact: Continuous/Ongoing
Mitigation Priority: 90 days
Inefficient License Utilization (SaaS Sprawl)
Risk Level: Medium
Potential Cost: $280K - $1.2M annually (wasted spend)
Time to Impact: Continuous/Ongoing
Mitigation Priority: 90 days
No Asset Recovery Process for Departing Employees
Risk Level: Medium
Potential Cost: $180K - $420K annually (ghost assets + security risk)
Time to Impact: Continuous/Ongoing
Mitigation Priority: 60 days
Manual Asset Tracking Processes
Risk Level: Low
Potential Cost: $95K - $210K annually (labor inefficiency)
Time to Impact: Continuous/Ongoing
Mitigation Priority: 180 days
No Central Repository for Purchase Orders and Warranties
Risk Level: Low
Potential Cost: $45K - $125K annually (missed warranty claims + inefficiency)
Time to Impact: Continuous/Ongoing
Mitigation Priority: 180 days
Use this framework to assess your current exposure:
Category 1: Financial Leakage (Max 30 points)
Do you know within 5% accuracy your total software licensing costs? (Yes = 0, No = 10)
Do you have automated license reclamation when employees depart? (Yes = 0, No = 10)
Can you identify unused/underutilized licenses within 30 days? (Yes = 0, No = 10)
Category 2: Security Posture (Max 40 points)
Do you have complete inventory of all network-connected devices? (Yes = 0, No = 15)
Can you patch critical vulnerabilities across all assets within 72 hours? (Yes = 0, No = 15)
Is shadow IT tracked and secured? (Yes = 0, No = 10)
Category 3: Compliance Readiness (Max 20 points)
Could you respond to a vendor audit with documentation in 48 hours? (Yes = 0, No = 10)
Do you maintain audit trails for all software deployments? (Yes = 0, No = 10)
Category 4: Operational Efficiency (Max 10 points)
Is new employee IT provisioning completed within 24 hours? (Yes = 0, No = 5)
Do you have strategic hardware refresh cycles? (Yes = 0, No = 5)
Your Risk Score Interpretation:
0-20 points: Low risk. ITAM optimization opportunities exist but no critical gaps.
21-50 points: Moderate risk. Strategic ITAM implementation recommended within 6 months.
51-75 points: High risk. Immediate ITAM implementation needed within 90 days.
76-100 points: Critical risk. Emergency ITAM project required. Consider interim security measures immediately.
| Criteria | Without ITAM | With ITAM |
|---|---|---|
| Financial Accuracy | Software spend variance of 25-35%. Ghost assets consume $420K+ annually. No visibility into TCO. Reactive crisis purchases at 40% premium. | Software spend accuracy within 3-5%. License utilization optimized at 92%+. Full TCO visibility drives strategic decisions. Volume purchasing saves 23% on hardware. |
| Security Posture | 40%+ shadow IT. Unknown devices on network. Patch compliance at 64%. Average breach cost: $8.9M. Time to detect breaches: 197 days. | Shadow IT below 12%. Complete device inventory. Patch compliance at 96%+. Average breach cost: $4.2M. Time to detect breaches: 73 days. |
| Compliance Readiness | Audit response time: 30+ days. Average audit penalty: $3.8M. Manual compliance documentation. Failed audits in 43% of cases. | Audit response time: 48 hours. Average audit penalty: $120K (86% reduction). Automated compliance reporting. Failed audits in <5% of cases. |
| Employee Productivity | Onboarding time: 8.3 days. Hardware downtime: 4.7 days average. IT support ticket volume: 847/month. Self-service capabilities: Limited. | Onboarding time: 2.1 days. Hardware downtime: 1.2 days average. IT support ticket volume: 312/month. Self-service capabilities: Extensive. |
| Strategic Value | IT viewed as cost center. No data for strategic planning. Firefighting consumes 60%+ of IT time. Technology debt accumulating. | IT positioned as strategic partner. Data-driven lifecycle planning. Proactive IT management at 75%+ of time. Technology debt actively managed. |
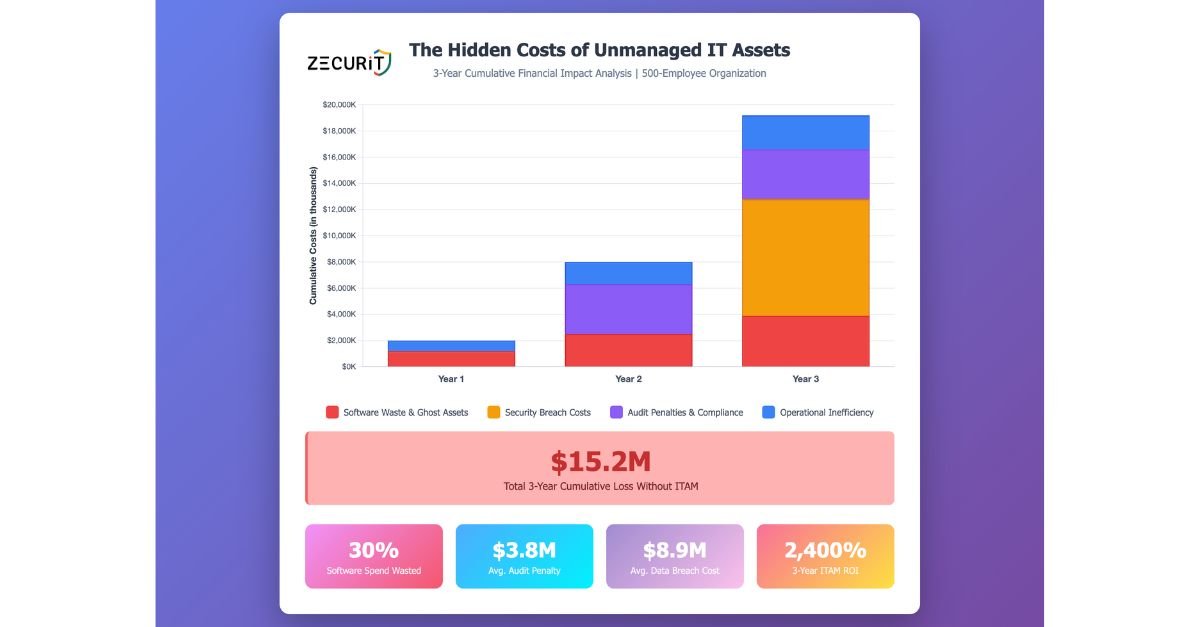
Annual Cost Impact for 500-Employee Organization:
Without ITAM: $4.2M - $8.7M in waste, penalties and inefficiency
With ITAM: $180K - $320K in software costs + recovered value of $3.8M - $7.9M
Net ROI: 1,200% - 2,400% over 3 years
Use this checklist in your next leadership meeting to assess ITAM readiness:
Scoring: Each checked box represents a documented risk area requiring executive attention.
0-3 boxes: Minor gaps. ITAM optimization recommended.
4-8 boxes: Moderate exposure. ITAM implementation should be prioritized.
9-15 boxes: Significant vulnerability. Immediate action required.
16+ boxes: Critical risk state. Emergency ITAM initiative needed.
Spreadsheets fail at managing IT assets for three fundamental reasons. First, they're outdated within 48 hours in dynamic environments where devices connect, software gets installed and employees join or leave. Second, they provide no automated discovery, meaning your spreadsheet only contains assets you manually enter, missing 30-40% of actual inventory. Third, they offer zero audit trail, integration capability or compliance automation.
Organizations with 50+ employees and 100+ assets reach the complexity threshold where manual tracking becomes more expensive than ITAM solutions. The cost of one software audit penalty ($3.8M average) exceeds 10-15 years of ITAM software investment. The question isn't whether you can afford ITAM, it's whether you can afford the next audit, breach or compliance failure without it.
ITAM delivers measurable ROI within the first year through four primary value drivers. License optimization alone recovers 15-30% of software spend by identifying unused licenses, eliminating redundancies and preventing auto-renewals. Security risk reduction decreases breach likelihood and associated costs averaging $8.9M per incident. Audit penalty avoidance saves $3.8M per vendor audit on average. Operational efficiency gains return 400+ hours of IT staff time annually by automating manual processes.
A typical 500-employee organization with $5M in annual IT spend achieves $750K-$1.5M in first-year value from ITAM implementation costing $180K-$320K. The ROI calculation is straightforward: for every dollar invested in ITAM organizations recover $3-$7 in the first year and $4-$12 over three years.
Modern ITAM solutions are specifically designed for resource-constrained IT teams through automated discovery, integration with existing tools and managed service options. Implementation typically requires 40-80 hours of IT involvement over 30-60 days, far less than the 400-800 hours annually spent firefighting asset-related issues without ITAM.
Many organizations actually reduce IT workload post-ITAM through self-service capabilities, automated provisioning and eliminating manual tracking efforts. If your IT team is too busy to implement ITAM, they're already overwhelmed by the operational chaos that ITAM would eliminate.
"Nothing's broken" is a dangerous assumption. Organizations typically discover their asset management failures during crises: vendor audits, security breaches, compliance failures or operational disruptions. By the time these events occur, the cost of remediation is 10-20x higher than proactive ITAM implementation.
Consider that you may not know what's broken. Can you answer these questions right now? What's your exact software licensing spend? Which devices are unpatched? How many licenses are unused? Where does personal data reside? If you cannot answer these questions with confidence, your current approach has hidden vulnerabilities that will eventually manifest as expensive incidents.
ITAM practices require underlying technology to be effective at scale. Manual processes and spreadsheets cannot provide automated discovery, continuous monitoring, integration with procurement and security tools, audit trails or compliance reporting required by modern IT environments.
Attempting ITAM practices without proper tooling creates "audit readiness theater", the illusion of control without actual visibility or compliance. Organizations pursuing this approach consistently fail audits, miss security threats and waste more money through inefficiency than they save by avoiding software costs. The math is clear: ITAM software costs $36-$64 per employee annually while recovering $1,000-$2,500 per employee through waste elimination.
The hidden costs of not having IT Asset Management are no longer hidden. This isn't about theoretical risks or future possibilities, these costs compound daily through financial leakage, security vulnerabilities, compliance exposure and operational inefficiency.
The evidence is unambiguous:
Organizations without ITAM waste 30% of their software spend annually. The average software audit penalty reaches $3.8 million. Security breaches cost $8.9 million when unmanaged assets serve as entry points. Operational inefficiency taxes productivity by $2.4-$6.7 million per year. These costs are cumulative, predictable and preventable.
The business case for ITAM is straightforward:
Implementation costs $180K-$320K for mid-sized organizations. First-year value recovery ranges from $750K-$1.5M. Three-year ROI reaches 1,200-2,400%. The question facing executives isn't whether ITAM provides ROI, it's whether you can justify another quarter without it.
Within 7 Days:
Complete the Executive Risk Checklist with your IT and Finance leadership
Calculate your organization's current software spend variance and ghost asset rate
Review your last vendor audit results (or assess when the next audit might occur)
Within 30 Days:
Conduct an ITAM readiness assessment using the Risk Score framework
Quantify the business case by calculating annual costs of financial leakage, security risk and operational inefficiency
Evaluate ITAM solutions appropriate for your organization size and complexity
Within 90 Days:
Implement ITAM solution or initiate implementation project
Establish baseline metrics for software spend, license utilization and security posture
Create quarterly executive reporting on ITAM value realization
Is the cost of implementing an ITAM solution lower than the cost of one major audit failure? The answer is definitively yes, by a factor of 10-20x. Is it lower than the cost of one security breach enabled by unmanaged assets? Yes, by a factor of 15-30x. Is it lower than one year of SaaS sprawl waste? Yes, by a factor of 3-7x.
The real question is: how much longer can your organization afford to operate without visibility, control and strategic management of its IT assets?
Gain real-time visibility into all your IT assets, automate network scans and ensure your organization’s security and compliance.