Connect to any device, any time, no end user required.
Patch servers at 2 AM, troubleshoot a remote workstation, or push software updates across a thousand endpoints without anyone
needing to "let you in."
Excellent
4.9/5
Traditional remote support requires someone at the other end to accept a connection request. That works fine during business hours, but IT doesn't operate on a 9-to-5 schedule.
Unattended remote access means you install a lightweight agent on the target device once. From that point forward, your team can connect instantly, any time, day or night, without prompting the device owner for permission.
No more scheduling maintenance windows around end-user availability. No more waking up a client to patch a critical vulnerability. No more delayed incident response because nobody is in the office.
"The average IT team loses 22 hours per month to scheduling delays alone. Unattended access eliminates that friction at the source, not with process, but with technology."
Faster average ticket resolution with unattended remote support
Device availability, maintenance on your schedule, not theirs
Install the agent once, connect forever, no re-authorizations
Manage thousands of endpoints from a single management console
Designed for speed, scale, and the real-world demands of modern IT infrastructure.
Connect to any endpoint at any hour. Servers, workstations, and laptops are always reachable, regardless of location or time zone.
Deploy Zecurit's lightweight agent once, via manual install, silent deployment, or GPO. After that, the device is permanently accessible without any further user interaction.
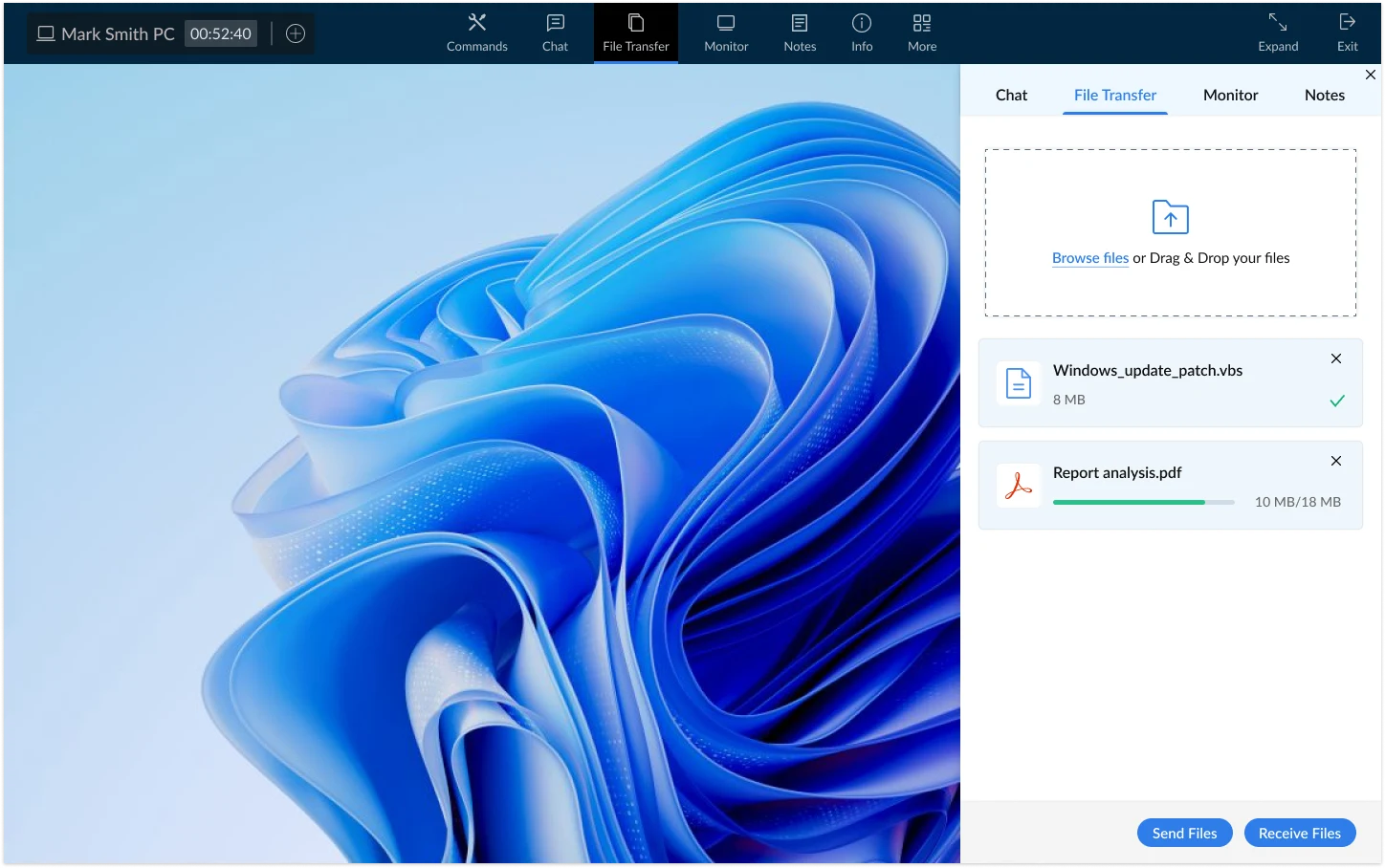
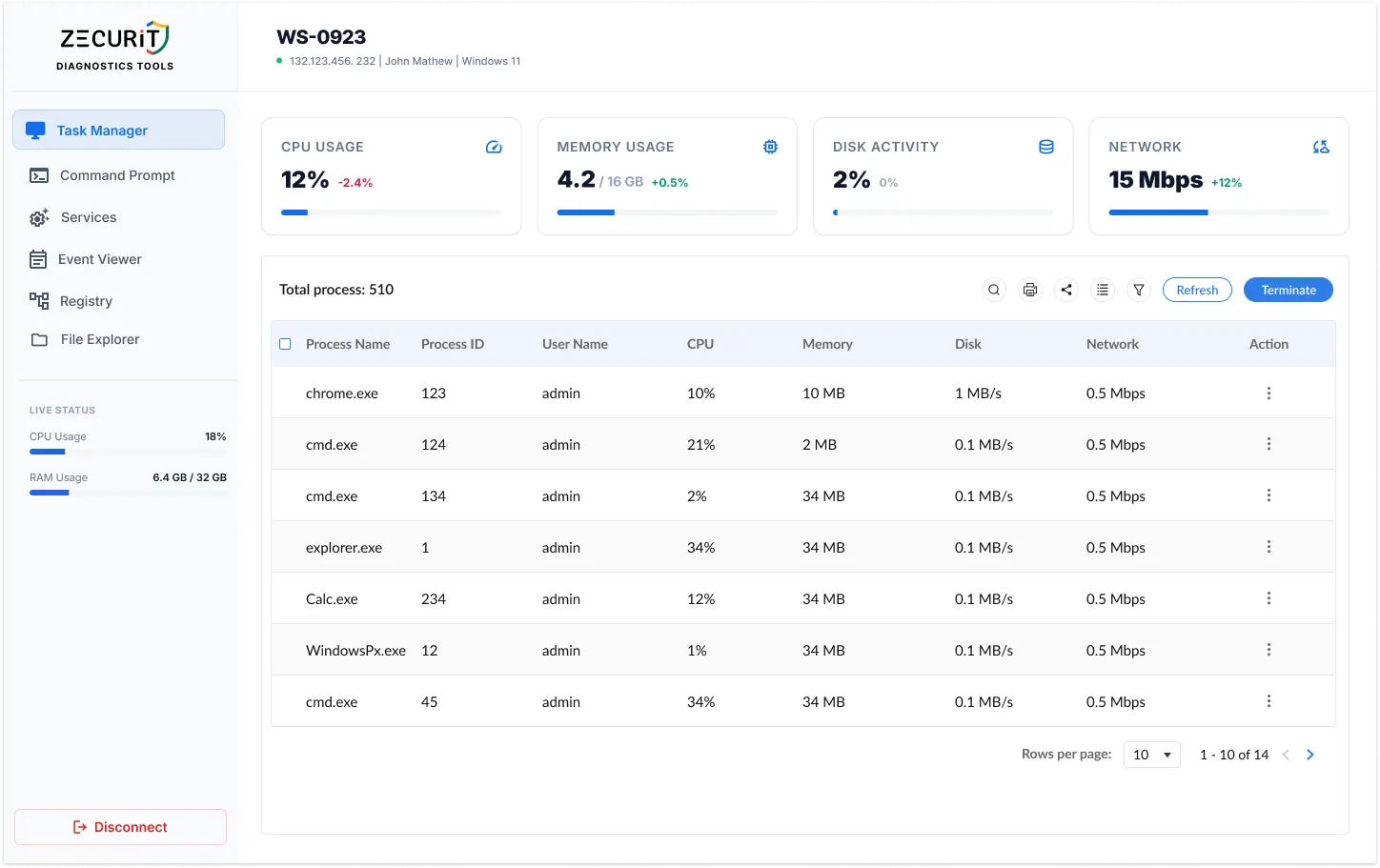
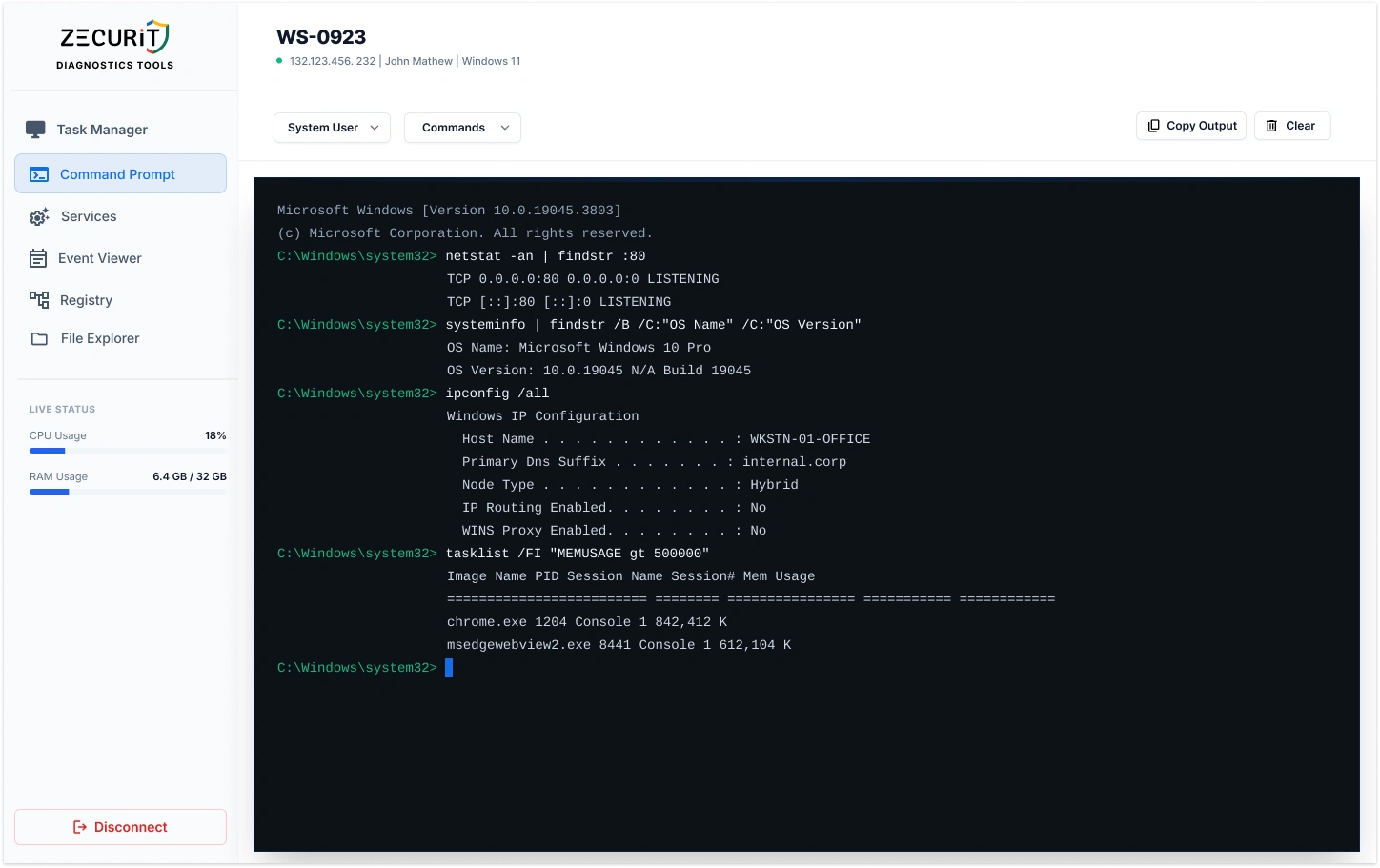
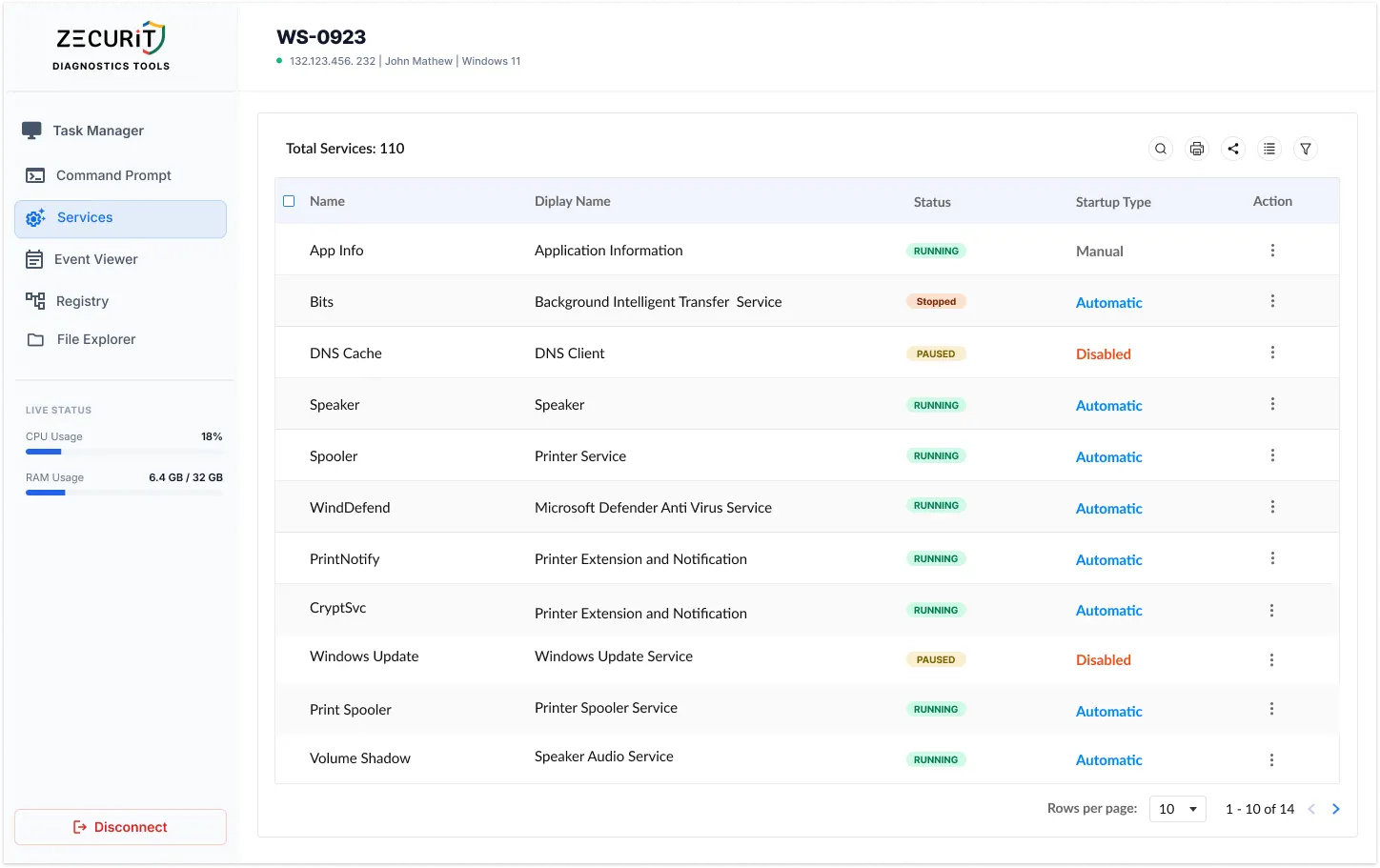
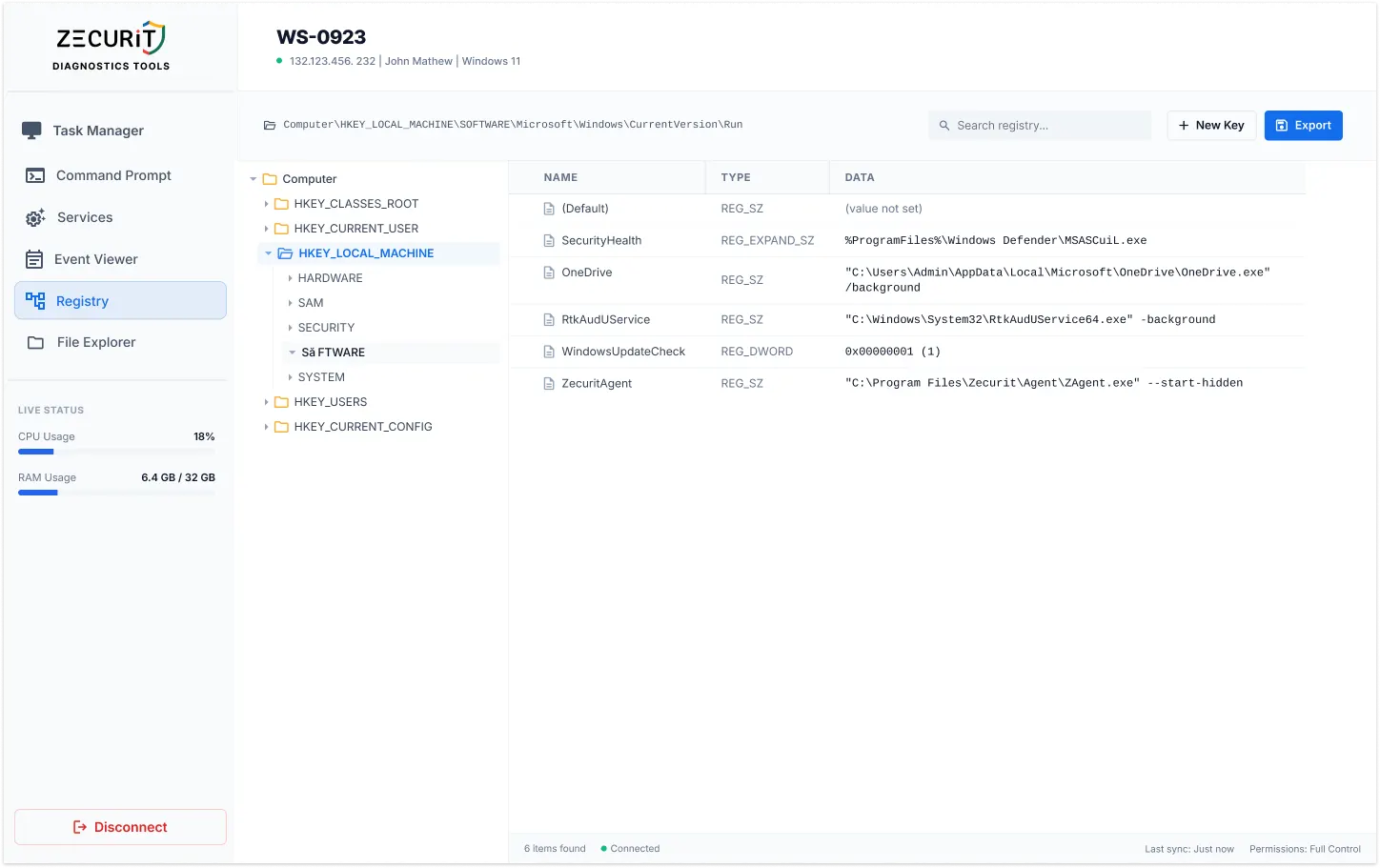
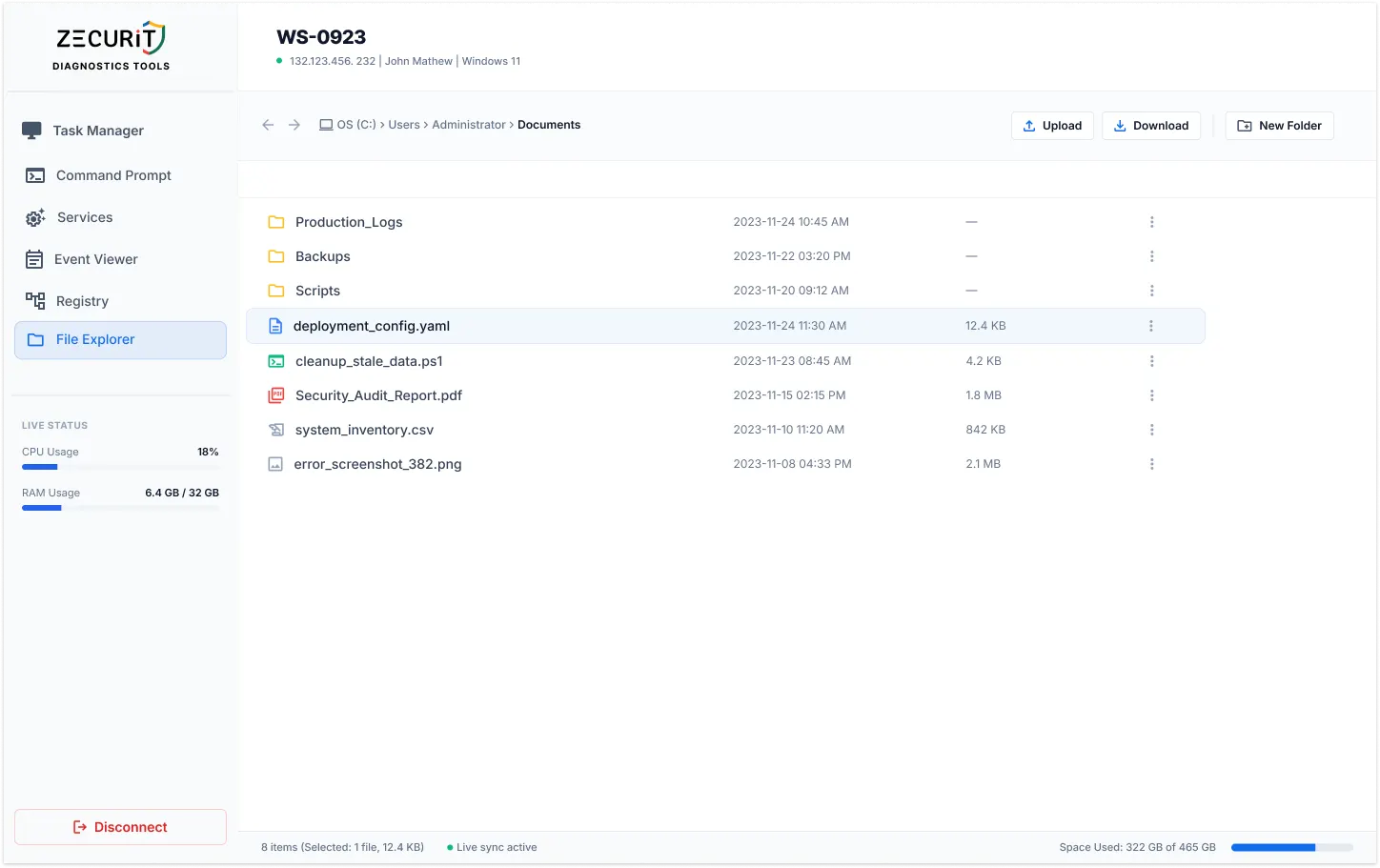
See and control the full remote desktop environment. Transfer files, run commands, manage processes, and reboot systems, all from a single interface.
Whether you manage 10 or 10,000 devices, Zecurit's unattended remote support infrastructure grows with you. No performance penalty at scale.
Every unattended session is logged with timestamps, actions taken, and technician identity. Compliance-ready out of the box.
Eliminate costly on-site visits. One technician can now support many more endpoints without additional headcount or travel expenses.
Security & Compliance
Unattended access without enterprise-grade security is just an open door. Zecurit closes it.
All remote sessions are encrypted in transit using TLS with AES-256. No unencrypted traffic ever leaves the endpoint. Your sessions are unreadable to anyone intercepting the connection.
Every unattended remote support session is automatically logged: who connected, when, what actions were taken, and for how long. Immutable audit trails support compliance audits and internal investigations.
Grant technicians access only to the devices they need. Junior support staff connect to tier-1 endpoints. Senior admins access servers. No over-provisioning, no lateral movement risk.
For devices where user consent is required, enable Session Confirmation. The end user must approve the connection before any unattended access begins, keeping you compliant with privacy policies.
No complex infrastructure. No open firewall ports. Just a lightweight agent and immediate access.
Sign up for Zecurit in under two minutes. No credit card required for the free trial. Your management console is ready immediately.
Install Zecurit's lightweight agent on target devices, manually, silently, or in bulk via GPO, Intune, SCCM, or Azure AD. Takes under 90 seconds per device.
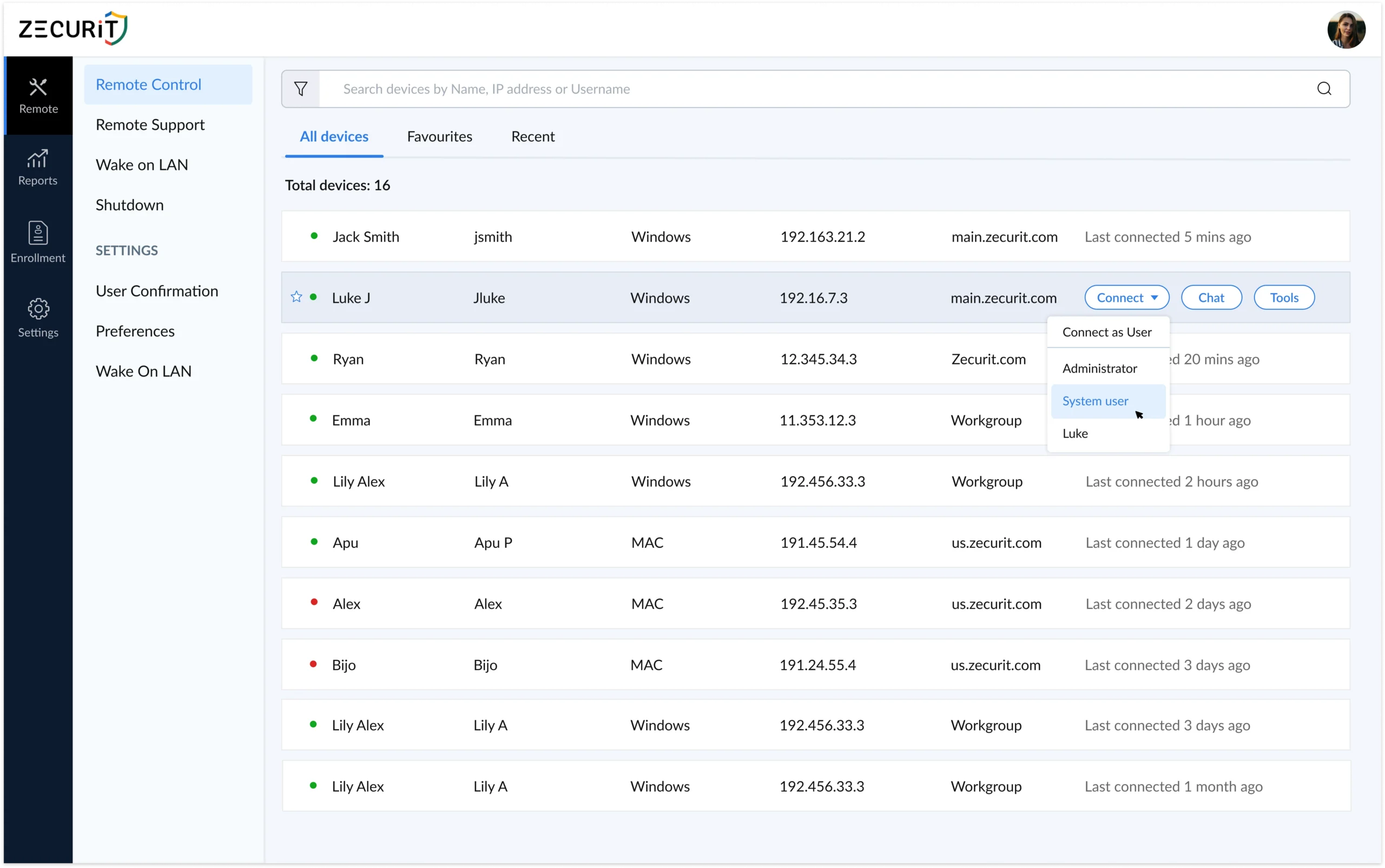
Once the agent is installed, devices register automatically. You'll see all endpoints in your centralized console , online status, OS type, last seen, and more.
Click any device to initiate an unattended remote desktop session. No user prompt. No waiting. Full control of the remote machine in seconds.
Both modes have a place in your IT toolkit. Here's when to use each and why Zecurit handles both.
Zecurit supports both modes from a single platform. Switch between unattended access and
attended remote support sessions in one click, no separate tools required.
Unattended remote access software lets IT teams connect to a device without requiring anyone to be present on the remote end. A lightweight agent is installed once, and from that point the device is always accessible. Standard remote desktop sessions — such as a basic Windows Remote Desktop connection — typically require someone to be logged in or to approve the connection. Unattended access removes that dependency entirely, making it essential for server administration, after-hours maintenance, and managing distributed endpoints across time zones.
Unattended remote access is safe when implemented correctly. Zecurit protects every session with AES-256 end-to-end encryption, mandatory MFA for all technician accounts, and role-based access controls that limit who can connect to which devices. No inbound firewall ports are opened on client machines, all traffic routes through Zecurit's secured cloud relay. Every session is logged with a full audit trail. For organizations that require user consent, Session Confirmation mode can be enabled to prompt end users before access begins.
Deploy Zecurit once. Access any device from anywhere, the moment you need it. No scheduling. No callbacks. No delays.