In a hybrid-cloud world where enterprises manage thousands of software licenses across on-premises data centers, SaaS platforms and multi-cloud environments, IT Asset Management (ITAM) has evolved from a back-office function to a strategic imperative. Yet many organizations still struggle with shadow IT, license compliance gaps and mounting software audit risks.
ISO/IEC 19770-1:2017 represents the international benchmark for ITAM excellence. Developed by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC), this standard provides a comprehensive framework known as the Management System for ITAM (MS-ITAM) that helps organizations establish trustworthy data, optimize software spend and demonstrate compliance to auditors, regulators and stakeholders.
Unlike vendor-specific methodologies, ISO 19770 is technology-agnostic and globally recognized. It transforms ITAM from reactive firefighting into a proactive governance discipline. For GRC professionals, IT directors and SAM managers, implementing this standard means moving beyond spreadsheet chaos to achieve measurable risk mitigation, cost optimization and operational excellence.
This guide demystifies the ISO 19770 family of standards and provides a practical roadmap to certification whether you're preparing for your first vendor audit or building enterprise-wide asset intelligence for the decade ahead.
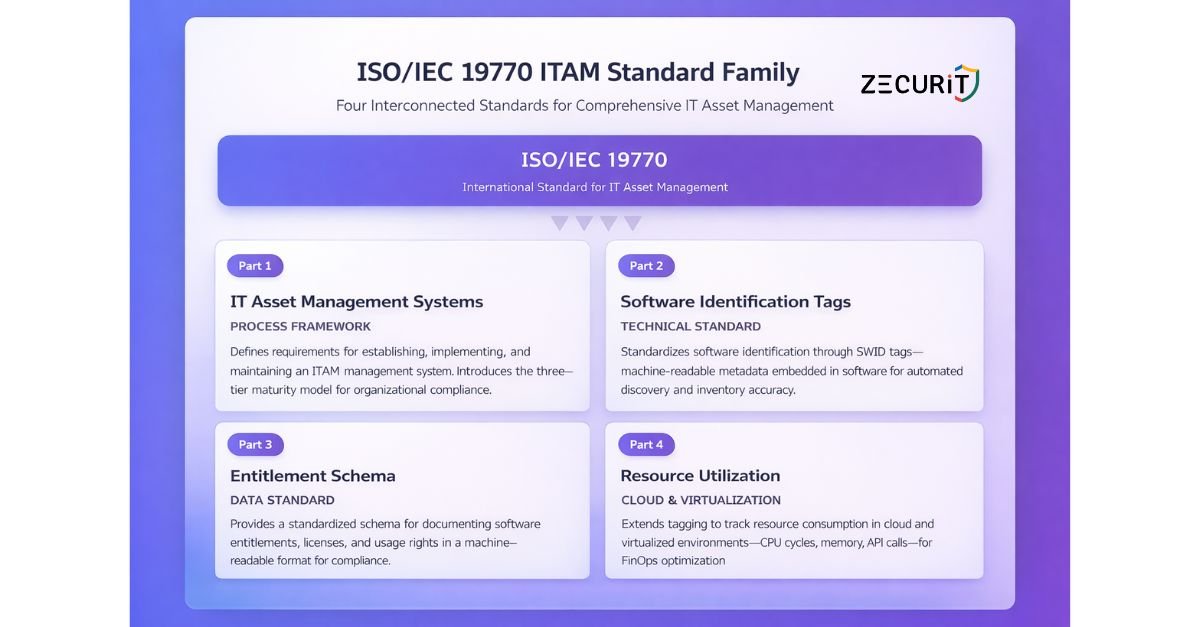
The ISO 19770 standard isn't a single document, it's a comprehensive family of interconnected specifications. Understanding how these parts work together is essential for building a cohesive ITAM strategy.
This is the cornerstone standard that defines requirements for establishing, implementing, maintaining and continually improving an ITAM management system. Think of it as the blueprint for your entire ITAM program. It introduces the three-tier maturity model (Trustworthy Data, Lifecycle Integration and Optimization) that organizations progress through on their certification journey.
ISO 19770-1 doesn't tell you which tools to use, it defines what processes you must have in place, from asset discovery and inventory management to software license reconciliation and compliance reporting. It's methodology-agnostic but outcome-focused.
Discovering what software exists in your environment is the first challenge of ITAM. Software Identification (SWID) tags solve this by embedding machine-readable metadata directly into software packages. These standardized tags contain product names, versions, publishers and unique identifiers.
When properly implemented, SWID tags enable automated software discovery and eliminate the guesswork of identifying applications through file hashes or executable names. Major software vendors now include SWID tags in their products, making inventory accuracy achievable at scale.
Knowing what you have installed is only half the equation, you also need to know what you're entitled to use. ISO 19770-3 provides a standardized schema for documenting software entitlements: the licenses, subscriptions and usage rights you've purchased.
This standard creates a common language for describing complex licensing terms (per-user, per-device, concurrent, cloud subscriptions) in a machine-readable format. When combined with SWID tag data, it enables accurate license compliance calculations and effective harvest-and-reuse programs.
Traditional software discovery tools struggle in virtualized and cloud environments where assets are ephemeral and dynamic. ISO 19770-4 extends the tagging concept to track resource consumption, CPU cycles, memory usage, API calls, in cloud and container environments.
For enterprises adopting FinOps practices, this standard provides the foundation for understanding true cloud utilization and optimizing spending based on actual consumption patterns rather than vendor estimates.
ISO 19770-1 introduces a tiered maturity model that allows organizations to progress incrementally rather than requiring perfection from day one. Each tier builds on the previous level.
Objective: Establish accurate, reliable and complete IT asset data.
Before you can manage assets effectively, you need to know what you have. Tier 1 focuses on creating a definitive source of truth for your IT asset inventory. This means implementing discovery tools, establishing data quality standards and reconciling information from multiple sources.
Key Requirements:
Strategic Value: Trustworthy data is the prerequisite for everything else. Without it, you're making decisions based on incomplete information, exposing your organization to compliance risks and wasted spending.
Common Pitfalls:
Objective: Integrate ITAM into standard IT processes throughout the asset lifecycle.
Having good data isn't enough if your processes allow it to become stale immediately. Tier 2 requires embedding ITAM activities into procurement, deployment, change management and decommissioning workflows. Assets should be tracked from requisition to retirement.
Key Requirements:
Strategic Value: Lifecycle integration transforms ITAM from periodic reporting to continuous governance. Assets are tracked in real-time, license compliance is proactive rather than reactive and the asset register remains perpetually accurate.
Objective: Use ITAM data to drive strategic decisions and measurable business value.
At the highest maturity level, ITAM becomes a strategic function that influences technology strategy, vendor negotiations and financial planning. Organizations at Tier 3 use asset intelligence for cost optimization, risk reduction and business innovation.
Key Requirements:
Strategic Value: Tier 3 organizations don't just avoid audit penalties, they actively reduce costs, negotiate better contracts, improve security posture and make data-driven technology decisions. ITAM becomes a revenue-protecting and cost-optimizing function.
| Tier | Objective | Key Requirements | Strategic Value |
|---|---|---|---|
| Tier 1: Trustworthy Data | Establish accurate asset inventory | Comprehensive discovery, data quality standards, regular reconciliation | Foundation for all ITAM activities; eliminates decision-making based on incomplete data |
| Tier 2: Lifecycle Integration | Embed ITAM in IT processes | ITSM integration, automated workflows, change management linkage | Real-time accuracy, proactive compliance, reduced manual effort |
| Tier 3: Optimization | Drive strategic business value | License optimization, vendor management, predictive analytics, executive reporting | Cost reduction, risk mitigation, data-driven technology strategy |
Achieving ISO 19770 certification is a structured journey. While timelines vary based on organizational size and current maturity, most enterprises complete certification within 12-18 months.
Before starting your certification journey, assess your current state against ISO 19770-1 requirements. Engage stakeholders across IT, procurement, finance and legal to understand existing processes, tools and pain points.
Key Activities:
Deliverable: A detailed gap analysis report with prioritized remediation items and a realistic timeline.
ISO 19770 requires formal documentation of your ITAM management system. This includes policies, procedures, roles and responsibilities and performance metrics.
Key Activities:
Deliverable: A complete MS-ITAM documentation package aligned with ISO 19770-1 structure.
With your management system designed, begin implementation. This phase involves tool deployment, process automation and organizational change management.
Key Activities:
Deliverable: A functioning ITAM environment with Tier 1 capabilities operational.
Before engaging external auditors, validate your implementation through internal audits. Identify non-conformities, implement corrective actions and demonstrate continuous improvement.
Key Activities:
Deliverable: Internal audit reports and evidence package demonstrating conformance.
Select an accredited certification body to conduct your external audit. The certification audit typically occurs in two stages: a documentation review followed by an on-site implementation audit.
Key Activities:
Deliverable: ISO 19770-1 certification valid for three years (with annual surveillance audits).
Pursuing ISO 19770 certification isn't about displaying a logo on your website, it's about building organizational capabilities that deliver measurable business value.
Accurate asset inventory is the foundation of cybersecurity. You cannot protect what you don't know exists. ISO 19770 ensures comprehensive visibility into all software assets, enabling effective vulnerability management and patch compliance. When security teams know exactly what's deployed and where, they can prioritize remediation based on actual exposure rather than guesswork.
Organizations with mature ITAM practices reduce their attack surface by identifying and removing unauthorized software, shadow IT and outdated applications that no longer receive security updates.
Software vendor audits are expensive, disruptive and increasingly common. Microsoft, Oracle, IBM, Adobe and SAP all conduct regular compliance audits that can result in penalties ranging from hundreds of thousands to millions of dollars for non-compliant organizations.
ISO 19770 certification demonstrates to vendors that you have robust license management processes in place. Many organizations report that vendors are less aggressive in their audit approach when they can demonstrate certification and some vendors offer preferred pricing or audit deferrals to certified organizations.
Cloud costs and software subscriptions represent rapidly growing expense categories. Without accurate utilization data, organizations over-purchase licenses "to be safe" or maintain unused subscriptions because nobody knows if they're still needed.
Tier 3 optimization practices enabled by ISO 19770 allow organizations to right-size their software portfolios based on actual usage. Enterprises commonly identify 20-30% savings opportunities through license harvesting, subscription optimization and elimination of redundant tools.
When renewal time arrives, organizations with ISO 19770-compliant ITAM practices negotiate from a position of strength. They can demonstrate actual deployment and usage data, challenge vendor claims about license requirements and make data-driven decisions about whether to renew, renegotiate orreplace solutions.
Beyond vendor audits, many industries face regulatory requirements around data governance, change management and configuration management (HIPAA, SOX, PCI-DSS, GDPR). ISO 19770 processes provide the asset intelligence and audit trails required to demonstrate compliance with these frameworks.
When auditors ask "How do you know what software is processing customer data?" or "Can you prove that unauthorized applications cannot be deployed?", ISO 19770-compliant organizations have documented, auditable answers.
ITIL 4 (IT Infrastructure Library) and ISO 19770 are complementary frameworks that address different aspects of IT management. Understanding their relationship helps organizations build comprehensive governance capabilities.
ITIL 4 provides best practices for IT service management, focusing on value co-creation, service value streams and continual improvement. It covers service strategy, design, transition, operation and improvement, but doesn't prescribe detailed processes for specific domains like asset management.
ISO 19770 provides the detailed requirements and processes specifically for managing IT assets throughout their lifecycle. It's more prescriptive than ITIL about what ITAM processes must exist and what outcomes they must achieve.
Modern IT organizations use ITIL 4 as their overarching service management framework and ISO 19770 as the detailed specification for their ITAM practice. Specifically:
Many organizations pursue ISO 19770 certification as part of their broader ITIL implementation, recognizing that excellent service management requires excellent asset management as its foundation.
Organizations that achieve ISO 19770 certification report quantifiable returns on their investment within 12-24 months. While implementation requires resources tool acquisition, staff training, process redesign the ongoing value far exceeds the initial cost.
Cost avoidance is the most immediate benefit. Avoiding a single major vendor audit penalty (often $500K-$2M+) typically justifies the entire ITAM program investment. Beyond penalty avoidance, license optimization commonly identifies 15-30% savings on software spending.
Operational efficiency improves when asset processes are automated and integrated. IT teams spend less time on manual inventory tasks, procurement cycles accelerate and compliance reporting becomes a matter of running reports rather than gathering data from multiple sources.
The less tangible but equally important benefits include improved decision-making (technology choices based on data rather than assumptions), enhanced security posture (knowing what you need to protect) and organizational credibility (demonstrating governance maturity to customers, partners and regulators).
ISO 19770 certification signals to stakeholders that your organization takes IT governance seriously. For organizations pursuing SOC 2, ISO 27001 orother security certifications, ITAM maturity becomes a supporting pillar of overall compliance programs.
As organizations grow through acquisitions, expand into new regions, or adopt new technologies, standardized ITAM processes scale more effectively than ad-hoc approaches. ISO 19770 provides the framework for onboarding acquired companies, extending asset management to new technology domains (IoT, OT, edge computing) and maintaining governance as complexity increases.
The initial investment in ISO 19770 creates lasting organizational capabilities that compound in value over time.
Use this checklist to evaluate your current ITAM maturity:
Tier 1: Trustworthy Data
Tier 2: Lifecycle Integration
Tier 3: Optimization
No, ISO 19770 certification is voluntary. However, many enterprises pursue certification to demonstrate governance maturity, satisfy customer requirements (especially in regulated industries), or differentiate themselves in competitive markets. Some organizations pursue certification as part of broader governance initiatives or in response to repeated vendor audit issues.
Alignment means implementing processes that follow ISO 19770 principles but without external validation. Organizations might describe themselves as "ISO 19770-aligned" when they've adopted the framework's best practices internally.
Certification requires an independent, accredited auditor to verify that your processes meet all ISO 19770-1 requirements and that you have evidence of effective implementation. Certification provides third-party validation and is typically renewed every three years with annual surveillance audits.
Many organizations start by pursuing alignment as they build capabilities, then pursue formal certification once they're confident in their implementation.
Traditional software discovery relies on identifying applications through file names, executables, or registry entries, methods that are error-prone and require constant updating as software evolves. SWID tags are standardized XML files embedded by software publishers that unambiguously identify the product, version, publisher and other metadata.
When discovery tools collect SWID tags, identification accuracy improves dramatically because you're using the publisher's own declaration rather than inferring identity from file patterns. This is particularly valuable for discovering cloud applications, containerized software and applications that don't follow traditional installation patterns.
Most organizations complete certification within 12-18 months from initial gap analysis to receiving certification. However, timelines vary significantly based on:
Small to mid-size organizations with focused scope can sometimes achieve certification in 8-12 months, while large enterprises with immature starting positions may require 18-24 months.
Certification costs vary based on organizational size and certification body, but enterprises should budget:
While not insignificant, these costs are typically offset by audit penalty avoidance and license optimization savings within the first 1-2 years.
Yes, though small businesses may not pursue formal certification. The principles of ISO 19770, accurate inventory, lifecycle management, license compliance, benefit organizations of all sizes. Small businesses face the same vendor audit risks and software cost pressures as large enterprises.
Rather than full certification, small businesses might adopt Tier 1 practices (trustworthy data) as their foundation, using the ISO 19770 framework as a roadmap without the expense of external audits. Many small businesses find that even basic implementation of ISO 19770 principles significantly improves their license compliance posture and readiness for vendor audits.
ISO 19770 compliance represents more than achieving certification, it's about transforming IT asset management from reactive administration into strategic governance. In 2026, as organizations navigate hybrid-cloud complexity, software-defined everything and increasing audit scrutiny, standardized ITAM processes aren't optional luxuries, they're business necessities.
The journey to ISO 19770 certification requires investment, commitment and organizational change. But the returns, improved security, reduced costs, audit readiness and data-driven decision-making, justify that investment many times over.
Whether you're just beginning to professionalize your ITAM practice or seeking to validate years of maturity-building efforts, ISO 19770 provides the roadmap. Start with trustworthy data, integrate ITAM into your operational fabric and ultimately achieve optimization that delivers measurable business value.
The question isn't whether your organization can afford to pursue ISO 19770 compliance, it's whether you can afford not to.
Discover how Zecurit automates ITAM processes and delivers Tier 1 data accuracy in weeks, not months.