| Framework | Primary Focus | Key Question It Answers | Best For |
|---|---|---|---|
| ITAM | Asset lifecycle & financial value | “What do we own and what does it cost?” | Procurement, budgeting, hardware tracking |
| SAM | Software license compliance | “Are we legal and optimized?” | Audit defense, license optimization |
| CMDB | Configuration relationships & operational state | “How is everything connected?” | Incident resolution, change management |
| ITSM | Service delivery & user experience | “How do we deliver value to users?” | Help desk, service catalog, SLA management |
If you're a new IT manager staring at vendor pitches that promise "complete visibility" through ITAM, SAM, CMDB or ITSM solutions, you're not alone in feeling overwhelmed. These four frameworks are often presented as overlapping, competing or identical concepts depending on who's selling what.
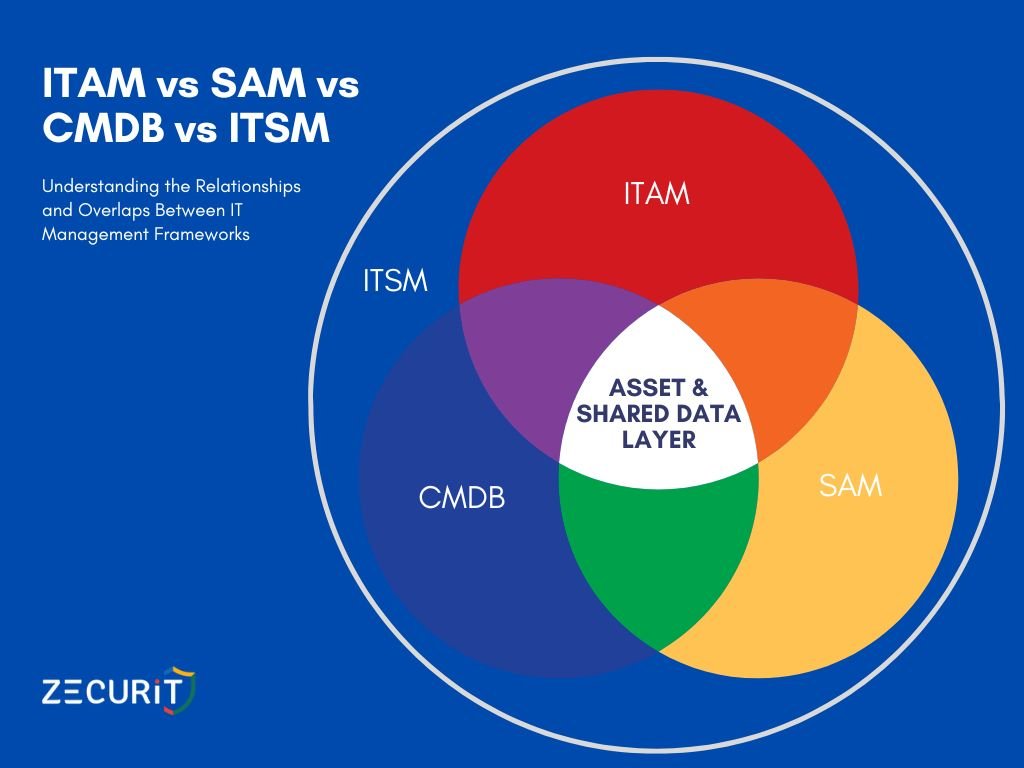
Here's the reality: They're not interchangeable and they're not competitors. They're complementary disciplines that serve distinct purposes while sharing common data. Understanding where each framework begins and ends is critical for making smart technology investments and avoiding the expensive trap of duplicate systems that don't communicate.
This guide cuts through the confusion with practical explanations, real-world scenarios and a decision framework to help you prioritize investments based on your organization's actual pain points. Whether you're facing failed audits, slow incident resolution or out-of-control IT spending, you'll leave with clarity on which approach delivers the fastest return on investment.
IT Asset Management is the comprehensive practice of tracking, managing and optimizing the full lifecycle of IT assets from acquisition through disposal. ITAM treats technology as financial investments that require oversight, maintenance and strategic planning.
ITAM answers one fundamental question: "What do we own, where is it and what is it costing us?"
This includes hardware (laptops, servers, mobile devices), software licenses, cloud subscriptions and even peripheral equipment like monitors and docking stations. The emphasis is on procurement cost, depreciation schedules, warranty tracking, total cost of ownership and ensuring you're not paying for unused or redundant assets.
ITAM professionals manage asset requisition and approval workflows, maintain accurate asset inventories with financial attributes, track maintenance contracts and warranties, plan for hardware refresh cycles and execute secure asset disposal processes that comply with data security regulations.
Your organization needs strong ITAM practices when you're experiencing budget overruns from unplanned IT purchases, difficulty answering "how many laptops do we actually have," challenges tracking warranty expirations leading to expensive out-of-warranty repairs or compliance issues with asset disposal and data wiping requirements.
Critical Distinction: ITAM focuses on the financial ownership and physical lifecycle of technology. It doesn't inherently track how these assets relate to each other operationally or how they support business services.
This is one of the most debated questions in IT governance. The answer is: It depends on your organization's maturity and complexity.
In smaller organizations, SAM often operates as a specialized function within ITAM. In enterprise environments with thousands of software licenses across multiple vendors, complex enterprise agreements and constant audit threats, SAM becomes its own dedicated discipline requiring specialized expertise.
Software Asset Management focuses exclusively on software license compliance and optimization. While ITAM tracks that you purchased 500 Microsoft Office licenses for $50,000, SAM ensures you're actually using 500 licenses (not 350 or 600), that you're compliant with licensing terms and that you're on the most cost-effective licensing agreement for your usage patterns.
SAM answers: "Are we legal and are we optimized?"
Organizations with mature SAM practices report 10-30% savings on software costs through license harvesting (reclaiming unused licenses), right-sizing subscriptions, avoiding audit penalties and negotiating better terms with vendors based on actual usage data.
SAM teams maintain a comprehensive software inventory with license entitlements, monitor actual software usage and installations, ensure compliance with vendor license agreements, manage software renewals and true-ups, defend against vendor audits and identify optimization opportunities like moving users from expensive licenses to cheaper alternatives.
Shadow IT when departments purchase software without IT approval is SAM's greatest challenge. That marketing team subscribing to a project management tool using a corporate card creates license compliance gaps, security vulnerabilities and redundant spending that SAM can't manage if it doesn't know the software exists.
Critical Distinction: SAM is about license compliance and cost optimization specifically for software. It requires deep knowledge of vendor licensing models, which are often more complex than simple "one license per user" equations.
A Configuration Management Database is a relationship map of your IT environment. It's less about "what we own" and more about "how everything connects and depends on each other."
The CMDB stores Configuration Items (CIs) which can be hardware, software, network components or even documentation and, more importantly, the relationships between these items.
This distinction trips up many IT professionals:
An Asset (ITAM) has financial value. You purchased it, it depreciates, it appears on accounting reports. Example: A Dell PowerEdge server purchased for $15,000.
A Configuration Item (CMDB) has operational value. It has a state (running, failed, in maintenance), relationships to other CIs and supports business services. Example: That same Dell server is running your customer database, connects to three application servers and supports your e-commerce service.
The same physical server can be both an asset (tracked in ITAM for financial purposes) and a CI (tracked in the CMDB for operational purposes). They're two different perspectives on the same object.
A properly populated CMDB answers: "How is everything connected and what's the blast radius of changes?"
When a network switch fails, the CMDB tells you which servers, applications and ultimately which business services are affected. When you need to patch a server, the CMDB shows you all the applications running on it and who depends on them. This is invaluable for change management, incident resolution and impact analysis.
According to research from industry analysts, approximately 70% of CMDB implementations fail to deliver expected value. The primary reason? Organizations build CMDBs without the foundational data discipline that comes from mature ITAM practices. You can't have accurate configuration relationships if you don't have accurate asset inventories to begin with.
A CMDB requires constant maintenance. Configuration items change state, relationships shift and new dependencies emerge. Without automation and strong data governance, CMDBs quickly become outdated and untrustworthy.
CMDB management includes discovering and documenting all configuration items in the environment, mapping relationships and dependencies between CIs, maintaining CI attributes (status, owner, location, specifications), tracking CI changes over time and supporting impact and dependency analysis for changes and incidents.
Critical Distinction: The CMDB focuses on operational relationships and service dependencies, not financial tracking or license compliance. It's the foundation for effective IT service delivery.
IT Service Management is the overarching philosophy and set of practices for delivering IT services that align with business needs. If ITAM, SAM and CMDB are ingredients, ITSM is the complete recipe for running an IT organization.
ITSM encompasses incident management (fixing problems), problem management (preventing recurrence), change management (controlling modifications), service catalog (what services IT offers) and service level management (defining and measuring performance commitments).
ITIL (Information Technology Infrastructure Library) is the most widely adopted framework for ITSM. ITIL 4, the current version, provides detailed best practices for service management processes. When organizations say they're "implementing ITSM," they're often implementing ITIL-based processes.
ITSM answers: "How do we deliver reliable, predictable IT services that support business objectives?"
This means your help desk can resolve incidents quickly because they understand service dependencies (CMDB), know what software licenses users should have (SAM), can track which hardware is assigned to whom (ITAM) and follow standardized processes for every interaction.
Mature ITSM includes a service desk as the single point of contact for users, an incident management process to restore services quickly, problem management to identify and eliminate root causes, change management to control modifications and reduce failures, a service catalog defining available services and how to request them and service level agreements defining performance commitments and measuring compliance.
Yes, but not effectively. You can run a help desk and manage incidents without a CMDB, but your technicians will work in the dark. They won't understand service dependencies, change impacts will be unpredictable and incident resolution will be slower because every issue requires manual investigation.
Think of it this way: You can drive without a GPS, but you'll take longer to reach unfamiliar destinations and make more wrong turns.
Critical Distinction: ITSM is the service delivery framework that uses data from ITAM, SAM and CMDB to deliver value to users. It's the orchestration layer that brings everything together.
Imagine running a restaurant. Here's how our four frameworks map to restaurant operations:
ITAM is your inventory and purchasing system. It tracks that you bought 50 pounds of chicken for $150, when it expires, which supplier you purchased from and that your walk-in refrigerator cost $8,000 and needs maintenance every six months. ITAM ensures you know what you own and what it costs.
SAM is your liquor license compliance program. You don't just track that you purchased 20 bottles of wine (that's ITAM). SAM ensures you have the proper liquor license for your jurisdiction, that you're storing alcohol according to regulations, that your staff are certified to serve it and that you're not violating any terms that could get you shut down or fined.
CMDB is your kitchen flow chart and recipe system. It documents that the chicken (an ingredient) is used in five different menu items, requires the grill and the sauté station, depends on the walk-in refrigerator staying cold and must be prepared by a certified cook. The CMDB shows how everything in your operation relates and depends on each other.
ITSM is your complete restaurant operation your service model, wait staff procedures, customer experience standards, how you handle complaints (incident management), how you train staff (change management) and what you promise on your menu (service catalog). ITSM is the entire system of delivering dining experiences to customers.
When the refrigerator breaks (an incident), ITSM processes kick in. Your staff check the CMDB to see which menu items are affected (anything with chicken, dairy or vegetables). They review ITAM records to find the warranty status and maintenance contractor. They might check SAM to ensure any diagnostic software used by the repair technician is properly licensed. This is integration in action.
Your ITAM system discovers and tracks physical and virtual assets. This inventory data flows into the CMDB, where assets become CIs with additional operational attributes and relationships. Without accurate ITAM data, your CMDB starts with garbage data and garbage in, garbage out applies ruthlessly to CMDBs.
When a help desk ticket arrives "Our CRM is down", the CMDB shows the service technician that the CRM application runs on three load-balanced servers, connects to a database cluster, depends on a specific network segment and supports the sales team's business process. This context transforms incident resolution from guesswork into informed troubleshooting.
Without SAM data, your help desk might provision software to users who don't have licensed entitlements, creating audit risks. Integration means service desk workflows check license availability before fulfilling software requests, automatically updating both SAM records and the CMDB when new software is deployed.
A new employee starts. HR creates their record. ITSM processes trigger an asset request. ITAM provisions a laptop from available inventory, updating financial records and asset assignments. The laptop becomes a CI in the CMDB, linked to the user and their department. SAM checks software entitlement rules and provisions appropriate licenses. The CMDB tracks these software installations as relationships to the laptop CI. The user's manager receives cost allocation reports from ITAM. When the user calls the help desk, agents see a complete picture: assigned hardware, installed software, service dependencies and cost information.
This is the power of integrated IT management frameworks.
Organizations often purchase separate tools for ITAM, SAM, CMDB and ITSM from different vendors with no integration strategy. This creates data silos where your help desk doesn't know what assets users have, your CMDB shows servers that were decommissioned months ago and your SAM team discovers compliance issues only during audits because they can't see actual software deployments.
Research from ITAM industry analysts indicates that organizations with integrated ITAM, SAM, CMDB and ITSM platforms report 40-50% faster incident resolution times, 25-35% reduction in software costs and significantly better audit outcomes compared to siloed implementations.
| Business Pain Point | Primary Solution | Why It Helps | Quick Win |
|---|---|---|---|
| Failed or feared audits | SAM | Establishes license compliance, usage tracking and documentation | License harvesting can fund the SAM program |
| Out-of-control IT spending | ITAM | Visibility into purchases, elimination of redundant assets, contract optimization | Find unused assets worth 10-20% of IT budget |
| Slow incident resolution | CMDB + ITSM | Dependencies and relationships accelerate troubleshooting | Reduce time-to-resolution by 30-40% |
| Change management failures | CMDB | Impact analysis prevents unexpected consequences of changes | Fewer failed changes means fewer incidents |
| Shadow IT proliferation | SAM + ITAM | Discovery tools find unauthorized purchases and installations | Identify redundant tools costing $50K-$500K annually |
| Poor user satisfaction | ITSM | Standardized processes and service commitments improve experience | Service catalog reduces confusion and request delays |
| Inability to answer “what do we have?” | ITAM | Foundational inventory and asset tracking | Accurate inventory in 90 days with automated discovery |
| Frequent security incidents | CMDB + SAM | Know what’s running where, ensure patches and licenses are current | Identify unpatched systems and unlicensed software |
Most mid-market organizations (500-5,000 employees) should follow this sequence for fastest ROI:
Phase 1: ITAM Foundation (Months 1-6). Implement automated discovery, establish baseline hardware and software inventory, document procurement processes and set up basic asset lifecycle workflows. This creates the data foundation everything else depends on.
Phase 2: SAM Compliance (Months 4-9, overlapping with ITAM). Once you know what software you have, establish license entitlement records, conduct initial compliance assessment, implement usage monitoring and prepare for vendor audits. The cost savings from SAM often fund subsequent phases.
Phase 3: ITSM Core Processes (Months 7-12). Implement or improve incident management, establish change management controls, create a basic service catalog and set initial service level agreements. These processes deliver immediate user experience improvements.
Phase 4: CMDB Build (Months 10-18). With ITAM data feeding accurate asset information and ITSM processes defining service requirements, build the CMDB using automated discovery and service mapping tools. Focus first on critical business services.
Phase 5: Integration and Optimization (Months 16-24). Connect all systems for seamless data flow, automate workflows across platforms, establish governance and data quality processes and continuously improve based on metrics and feedback.
You don't need to implement all four frameworks simultaneously. In fact, attempting to do so usually leads to failure. Start with the area causing the most pain and delivering the fastest return. Use savings and credibility from early wins to fund subsequent phases.
A Single Source of Truth means every piece of IT data lives in one authoritative location, is maintained through defined processes and is accessible to all systems and teams that need it. Without SSOT, you get conflicting information: your ITAM system shows 500 laptops while your CMDB shows 487 and your help desk system shows 523 assigned devices.
Building SSOT doesn't necessarily mean one giant platform that does everything. Many successful organizations use a federated model where ITAM is the authoritative source for asset financial data, SAM owns license entitlement and compliance data, the CMDB is authoritative for operational state and relationships and ITSM pulls from these sources to deliver services.
The key is establishing clear data ownership, implementing real-time or near-real-time integration between systems, enforcing data quality standards across all platforms and preventing manual data entry in multiple places.
Modern integration platforms and APIs make federated SSOT possible. When you purchase a laptop through your procurement system (ITAM), that transaction automatically creates or updates the asset record, which flows to the CMDB as a new CI, triggers ITSM workflows for deployment and updates cost allocation reports, all without manual data entry.
Organizations fail at SSOT when they designate the wrong system as authoritative for specific data types (like making ITSM the master for asset financial data), implement one-way integrations that create data conflicts, allow exceptions and manual workarounds that undermine data quality or lack governance to maintain SSOT integrity over time.
Successful SSOT requires governance: defined data owners for each domain, data quality metrics and monitoring, regular audits to identify and correct discrepancies, change control for modifications to integration logic and clear escalation paths when data conflicts arise.
Think of data governance as the constitution for your IT data. It defines who has authority, how conflicts are resolved and what standards everyone must follow.
Answer these questions honestly about your organization:
Question 1: Asset Visibility
If you answered "No" to any Question 1 items: START WITH ITAM
Question 2: Software Compliance
If you answered "No" to Question 2-1, "Yes" to 2-2 or "No" to 2-3: PRIORITIZE SAM
Question 3: Service Delivery
If you answered "No" to any Question 3 items: FOCUS ON ITSM
Question 4: Change Management
If you answered "No" to 4-1, "Yes" to 4-2 or "No" to 4-3: YOU NEED A CMDB
Organizations typically need multiple frameworks, but this assessment helps you sequence investments:
If you need ITAM: Start here. Everything else depends on accurate asset data.
If you need SAM and passed Question 1: SAM is high priority, but ensure ITAM is at least minimally functional first.
If you need ITSM but failed Question 1: You'll get limited value from ITSM without basic asset visibility. Address ITAM concurrently.
If you need CMDB but failed Questions 1 or 3: Building a CMDB without ITAM data and ITSM processes to maintain it will likely fail. Address foundations first.
Small organizations (Under 250 employees): Start with ITAM covering both hardware and software. Add ITSM processes next. You may never need a formal CMDB if your environment is simple.
Mid-market (250-2,500 employees): Follow the phased approach outlined in the Decision Matrix section. You need all four frameworks eventually.
Enterprise (2,500+ employees): You likely need dedicated teams and platforms for ITAM, SAM, CMDB and ITSM, with significant integration efforts to maintain SSOT.
The confusion between ITAM, SAM, CMDB and ITSM is understandable, they overlap, integrate and share data in complex ways. But understanding their distinct purposes is critical for making smart technology investments and building effective IT management capabilities.
Remember the core distinctions: ITAM tracks financial value and lifecycle, SAM ensures software compliance and optimization, CMDB maps operational relationships and dependencies and ITSM orchestrates service delivery using data from the other three.
You don't need perfection in all four areas simultaneously. Start with your most pressing pain point, deliver results and build from there. Each framework strengthens the others, creating compound benefits as your IT management maturity increases.
The organizations that succeed are those that view ITAM, SAM, CMDB and ITSM not as competing alternatives but as complementary pieces of a complete IT management strategy. When these frameworks work together, feeding each other accurate data and supporting integrated workflows, they transform IT from a cost center reacting to problems into a strategic enabler driving business value.
Your journey from IT acronym confusion to management clarity starts with one step: honestly assessing your current state and choosing the framework that addresses your most critical challenge. From there, each success builds momentum for the next improvement, eventually creating the integrated, efficient and strategically aligned IT organization your business deserves.
Organizations using Zecurit recover an average of $150K annually through license optimization and asset reclamation.