Zecurit’s real-time endpoint alerting engine detects hardware changes, software installs, disk issues, and security threats, and notifies your team before users even notice.
Alert Categories
Monitorable Conditions
Severity Levels
Policy-Driven Automation
Create a policy, define your conditions, associate it with device groups and let Zecurit do the watching.
Name your policy, set its priority level (Critical, High, Medium, or Low), and configure the notification email. Each policy acts as a reusable ruleset that can be applied across multiple device groups.
Choose from Hardware, Software, License, Certificates, Disk Space, and Security scan conditions. Mix and match triggers, from USB additions to expired SSL certs in a single policy.
Link the published policy to one or more device groups. Zecurit immediately begins monitoring every enrolled endpoint against your defined conditions and fires alerts the instant a threshold is crossed.
From a new GPU in a server to an untrusted root certificate — Zecurit covers every layer of your endpoint stack.
Track hardware lifecycle events and configuration shifts - monitor component changes to maintain hardware integrity and performance.
Stay informed of high-priority software events, enforce compliance and security by monitoring installation changes and prohibited application activity in real-time.
Monitor license health to ensure legal compliance and optimize software spend by identifying usage gaps.
Proactively manage your digital trust, prevent service outages by monitoring expiration timelines and identifying non-standard encryption sources.
Prevent system downtime and data loss, monitor storage health by setting proactive triggers for critical capacity limits across all drives.
Maintain a constant defensive posture, instantly detect vulnerabilities when core protection services are disabled or compromised.
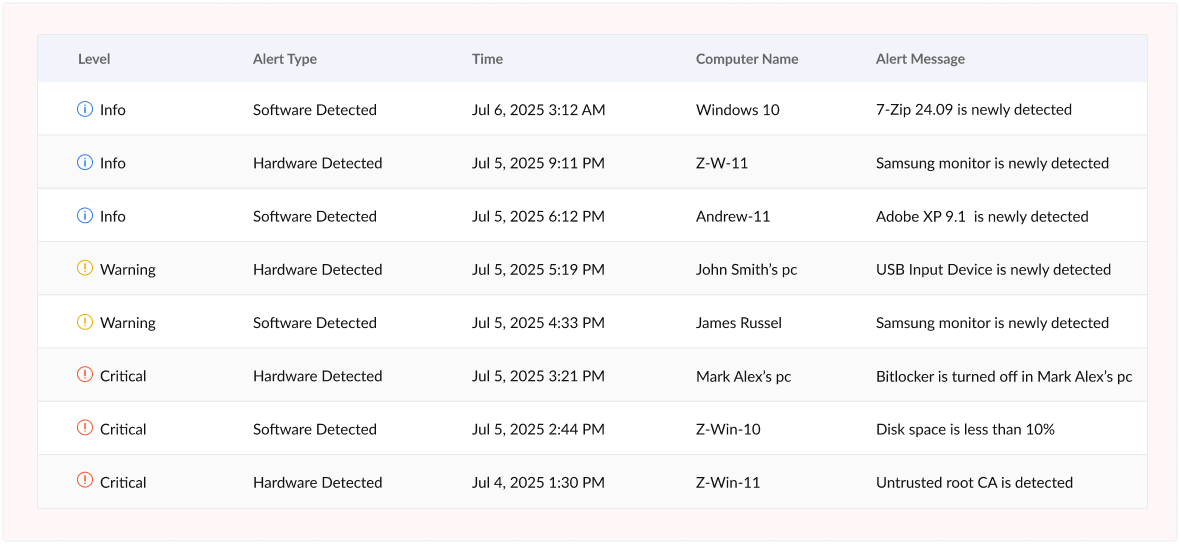
Not all events are equal. Zecurit separates the noise from the genuine threats with four priority tiers, so your team always knows what to tackle first.
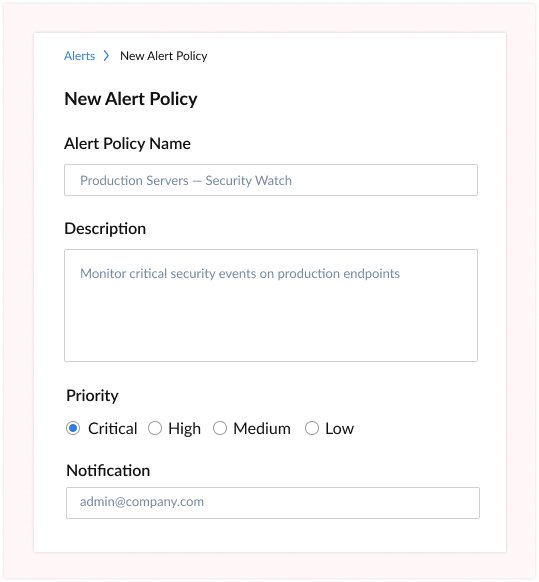
Zecurit's guided policy wizard makes it simple to configure exactly what you want to monitor, at what threshold, and who gets notified, no scripting required.
Endpoint alert management isn't just about fires, it's about preventing them before they start.
Get instantly notified when BitLocker or FileVault is disabled on any endpoint, when antivirus services stop running, or when an untrusted root certificate appears. Catch compliance failures in minutes, not months.
Alert your team the moment an unapproved USB device, external monitor, or network adapter is added to a managed machine. Protect data and enforce hardware policy across your entire device fleet.
Detect prohibited software the instant it is installed on any endpoint. Track license expiry windows and over/under-licensed conditions to stay audit-ready at all times, with zero manual checking
Stop users from hitting storage walls. Set percentage-based thresholds on both overall and individual drive utilization. Receive alerts with enough lead time to clean up, archive, or expand capacity.
Configure advance warning days for expiring SSL/TLS certificates and software licenses. Eliminate embarrassing certificate-expiry outages and unexpected licensing gaps with automated early alerts.
Every hardware addition, software install, and security state change is logged with a precise timestamp and computer name. Use the alerts log as your lightweight change management and IT audit trail.
An Alert Policy in Zecurit is a named ruleset that specifies which conditions trigger alerts on endpoints, such as low disk space, hardware changes, or security service failures. Policies must first be created and then associated with device groups to become active. Once linked, Zecurit continuously evaluates enrolled devices against the policy conditions during each inventory scan.
Yes. Zecurit is designed for multi-group environments. You can create distinct alert policies, for example, a stricter security policy for servers and a lighter hardware-change policy for workstations — and associate each policy with the relevant device group via the Associate Policy feature.
Zecurit can monitor over 15 hardware categories including Audio, Battery, BIOS, Keyboard, Monitors, Motherboard, Pointing Devices, Printers, USB Controllers, USB Hubs, TPM, Network Adapters, Physical Memory, Hard Disks, Processors, and Video Controllers, detecting both additions and removals during inventory scans.
Zecurit supports both overall disk space alerts and individual drive alerts. You can configure percentage-based thresholds (e.g., trigger when overall disk space falls below 10%). Thresholds are set within the alert policy and can be updated at any time, changes apply to all associated device groups immediately.
Yes. Zecurit's certificate monitoring can alert you a configurable number of days before a certificate expires, as well as detect self-signed certificates and untrusted root CAs. For software licenses, it can alert on expired licenses, licenses nearing expiration within a defined window, under-licensed software, and over-licensed software.
Set up your first alert policy in minutes. Zecurit watches your endpoints around the clock so you don't have to.
Discover the powerful modules that help you manage, secure, and control every endpoint from a single console.
Gain full visibility into hardware and software assets across your organization.
Remotely deploy and manage applications across devices with ease.
Automate patch scanning and deployment to keep endpoints secure and compliant.
Securely access devices, troubleshoot issues, and support users from anywhere.
Enforce IT policies and maintain standardized configurations across endpoints.
Generate endpoint reports and audit trails to monitor compliance and activity.