What is Endpoint Security? Complete Guide for 2025
Learn what endpoint security is, why it’s critical for protecting business devices, and how it differs from traditional antivirus.
This article provides detailed information about supply chain attacks, which exploit vulnerabilities in third-party suppliers to compromise end-user systems.
In today’s hyper-connected digital landscape, businesses are leaning more than ever on third-party vendors, software and services to keep things running smoothly. But this heavy reliance also opens the door to a major risk: supply chain attacks. These intricate cyberattacks exploit the trust we place in our external partners to breach target organizations, often resulting in serious consequences.
In this article, we’ll explore how supply chain attacks work, their impacts and how to prevent them, offering practical tips for cybersecurity professionals
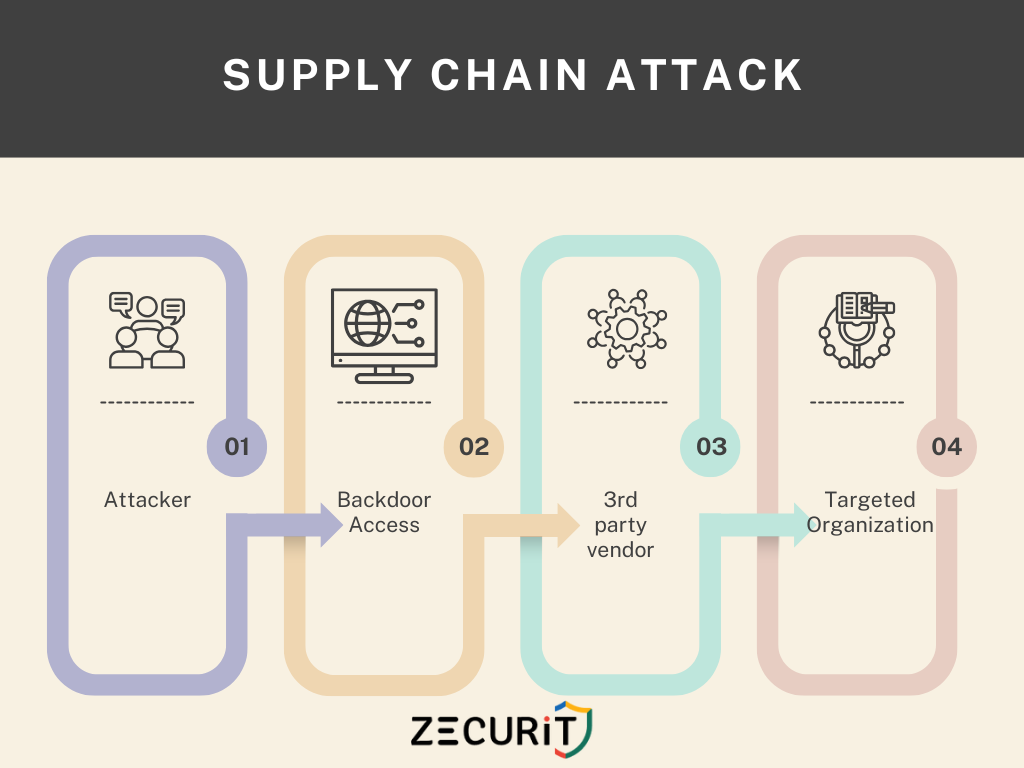
A supply chain attack occurs when cybercriminals targets a trusted vendor, supplier, or service provider to infiltrate a larger organization’s network. Instead of going after the target directly, these attackers exploit vulnerabilities in the supply chain like third-party software, hardware or services to inject malicious code, steal sensitive data or disrupt operations. These attacks are particularly dangerous because because they can bypass standard security measures by utilizing legitimate channels.
Real-World Examples:
According to ENISA, supply chain attacks skyrocketed by four times in 2021, and Gartner predicts that by 2025, 45% of organizations will face such threats. As attackers become increasingly sophisticated, it’s vital for organizations to bolster their supply chain resilience. Taking proactive steps like conducting vendor audits, adopting secure coding practices and implementing zero-trust policies has transitioned from being a nice-to-have to a must-have.
Cybersecurity Ventures estimates that the global annual cost of software supply chain attacks will reach $60 billion by 2025 and could soar to $138 billion by 2031, with an annual growth rate of 15%.
Supply chain attacks represent a major shift in the cybersecurity landscape, exploiting established trust to inflict serious damage. By understanding how these attacks operate and putting robust prevention strategies in place, organizations can fortify their defenses against this escalating threat. In an era where digital interdependence is a given, staying vigilant and collaborating is crucial for safeguarding the supply chain.
A supply chain attack occurs when cybercriminals compromise a trusted vendor, software, or service provider to infiltrate a target organization’s network. Attackers exploit vulnerabilities in third-party tools to deliver malware or steal data.
Attackers compromise a vendor (e.g., software developer), inject malware into legitimate updates or tools, and distribute them to victims. Once deployed, the malware steals data, deploys ransomware, or disrupts operations.
They exploit trusted relationships and hide within signed, legitimate software. Traditional security tools often miss these threats because they appear as routine updates.
An SBOM is a detailed inventory of all components (e.g., libraries, frameworks) in software. It helps identify vulnerabilities in third-party code, as mandated by recent U.S. cybersecurity regulations.
Learn what endpoint security is, why it’s critical for protecting business devices, and how it differs from traditional antivirus.
HIPAA compliance is mandatory for healthcare organizations and their vendors to protect sensitive patient data (PHI/ePHI). This guide explains cybersecurity requirements like encryption, access controls, and breach protocols, along with penalties for violations. Learn how IT teams, sysadmins, and HelpDesk staff can implement HIPAA best practices.
Supply chain attacks target third-party vendors to infiltrate organizations, bypassing traditional defenses. Learn how these attacks work, their devastating impacts (e.g., SolarWinds), and actionable strategies to defend your business.