How intelligent automation, self-healing workflows, and policy-driven enforcement are replacing manual IT operations and defining the next era of endpoint governance.
Updated: March 2026
Autonomous Endpoint Management (AEM) is the use of intelligent, policy-driven automation to continuously discover, manage, secure, and remediate every endpoint in an organization's environment without requiring human intervention for routine operations. Where traditional Unified Endpoint Management (UEM) gives administrators tools to act, AEM gives the platform the authority to act based on pre-defined intent, real-time telemetry, and risk-based decision logic.
The word "autonomous" is precise and deliberate. AEM does not mean IT teams lose visibility or control. It means the platform executes the decisions that administrators would have made anyway, faster and at a scale that human operators cannot match. A fleet of 5,000 endpoints generates thousands of state changes per day: patches released, configuration drift events, new devices enrolling, services failing, disk space degrading, security agents going stale. AEM processes and responds to every one of these events continuously, while the IT team focuses on architecture, strategy, and the exceptions that genuinely require human judgment.
According to Gartner's trajectory toward Autonomous Endpoint Management, the defining characteristic of AEM in 2026 is the shift from reactive tooling (an admin sees a problem and fixes it) through proactive automation (the platform detects and alerts) to autonomous remediation (the platform detects, decides, and fixes without waiting for a human in the loop). Most organizations in 2026 operate somewhere between proactive and autonomous. The gap between where they are and full autonomy is measurable in security risk, operational cost, and engineering capacity.
The most important distinction in the AEM conversation is not between old tools and new tools. It is between two fundamentally different operating philosophies.
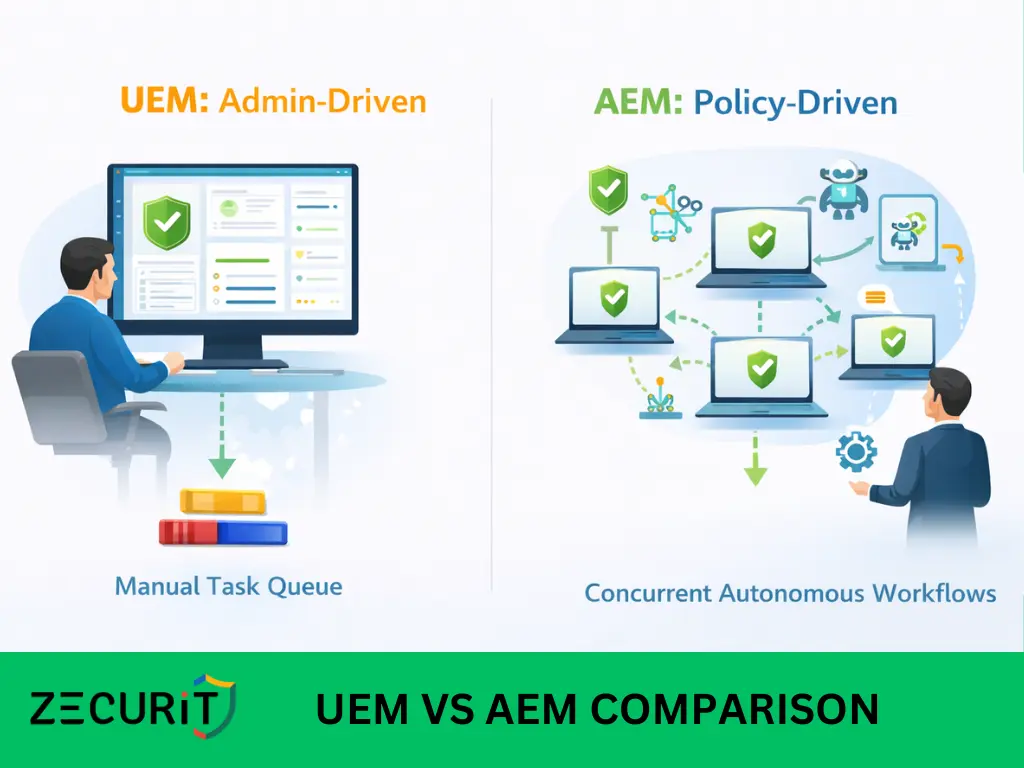
In a UEM environment, the platform provides visibility and tools. A missing patch appears in a dashboard. An administrator reviews it, approves deployment, schedules it, monitors execution, and reviews the compliance report. Each step requires a human decision and a human action. The platform is a tool; the administrator is the engine.
In an AEM environment, the administrator defines intent: "critical patches must be deployed within 72 hours," "BitLocker must always be enabled," "disk usage must never exceed 90%," "the security agent must always be running." The platform monitors every endpoint continuously against these intent statements and executes remediation automatically when a deviation is detected. The administrator is the architect of policy; the platform is the engine that enforces it at machine speed.
The operational consequence of this gap is significant:
| Scenario | UEM Response Time | AEM Response Time |
|---|---|---|
| Critical CVE patch released | Days to weeks (admin review, approve, schedule, deploy) | Hours: Auto-approved by severity rule, staged ring deployment executes |
| BitLocker disabled on a device | Next compliance scan cycle detects it, admin notified, manually re-enabled | Minutes: Detected within minutes, auto-remediated, compliance event logged |
| Disk usage exceeds 85% threshold | Alert fires, admin creates ticket, scheduled cleanup | Immediate: Self-healing script triggers automatically, temp files cleared, alert resolved |
| New device enrolls with no agent | May not be discovered for days if not manually inventoried | Immediate: Auto-discovered, enrollment triggered, baseline applied |
| Security service stops unexpectedly | Alert fires, admin investigates, manually restarts service | Immediate: Watchdog script detects service down, restarts automatically, logs the event |
| Configuration drift from security baseline | Detected at next scan, admin remediates manually | Real-Time: Drift detected in real time, auto-remediated to baseline, drift event logged |
The cumulative effect of this difference across thousands of devices and hundreds of events per day is the business case for AEM. Mean Time to Remediate (MTTR) drops from days to minutes. Security posture is maintained continuously rather than between audit cycles. Engineering capacity is redirected from reactive firefighting to strategic initiatives.
A Forrester study on IT automation ROI found that organizations implementing hyper-automation across IT operations reduced incident response time by up to 70% and reclaimed an average of 25% of IT engineering capacity for higher-value work. AEM is the application of that same hyper-automation principle to the endpoint layer specifically.
| Dimension | Stage 1: Manual IT | Stage 2: Managed IT (UEM) | Stage 3: Autonomous IT (AEM) |
|---|---|---|---|
| Patching model | Manual SSH or fragile cron jobs | Admin-approved, console-deployed | Risk-scored auto-approval, staged auto-deployment |
| Compliance | Point-in-time audits | Dashboard visibility, admin action | Continuous enforcement, auto-remediation on drift |
| Inventory | Static spreadsheets or periodic scans | Agent-reported, updated on check-in | Real-time, continuous, self-updating, shadow discovery |
| Incident response | Reactive, ticket-driven, sequential | Alert-driven, admin-initiated | Self-healing scripts resolve before ticket is raised |
| Software deployment | Manual install or Ansible playbooks | Console-initiated, admin-targeted | Intent-based: enrollment triggers auto-deployment |
| Security posture | Manual hardening, infrequent review | Policy enforcement, periodic scans | Continuous drift detection, instant auto-remediation |
| Scalability | Fails above 50 to 100 nodes | Scales with admin overhead | Scales to 10k+ with constant IT headcount |
| MTTR | Days to weeks | Hours to days | Minutes to hours |
| Human role | Operator (executes) | Manager (approves/monitors) | Architect (defines policy) |
The shift from Stage 2 to Stage 3 is where most enterprise IT organizations need to focus in 2026. The tooling exists. The policy frameworks exist. The gap is a deliberate decision to move from administrator-driven operations to policy-driven autonomy and a platform that makes that transition practical.
No autonomous system can remediate what it cannot see. Continuous inventory is the foundational prerequisite for every other AEM capability. It is not a periodic scan or a scheduled report. It is a real-time, always-current data model of every endpoint's hardware configuration, installed software, running services, security state, user activity, and network connectivity.
In the AEM context, inventory serves three functions that go beyond its traditional asset management role.
Shadow device discovery. Autonomous management cannot be limited to devices that IT knows about. Any unmanaged device on the network is a blind spot, a potential attack vector, and a compliance gap. Continuous inventory includes automated network discovery that identifies devices without management agents, flags them in the console, and can trigger automated enrollment workflows for devices that match defined criteria.
The telemetry foundation for autonomous decisions. Every AEM automation rule draws on inventory data as its trigger. "IF disk usage exceeds 85%" requires real-time disk usage data. "IF the security agent is not running" requires real-time process monitoring. "IF the OS version is more than two patch levels behind" requires real-time OS version data. The quality and freshness of inventory data directly determines the accuracy and timeliness of autonomous remediation.
Compliance posture as a living state. In traditional UEM, compliance posture is assessed periodically and reported historically. In AEM, compliance posture is a live attribute of every device, updated continuously as configuration state changes. When a device falls out of compliance, the compliance state changes immediately, which triggers the remediation workflow, which resolves the issue, which returns the device to compliance, all within minutes and without any administrator action.
Zecurit's IT asset management provides the real-time inventory foundation for autonomous workflows: hardware specifications, installed software with version tracking, running services and processes, network interfaces, and security posture state, all reported continuously from the lightweight agent to the central console.
Zero-touch patching is the AEM capability that delivers the most immediate and measurable security ROI. It is the complete automation of the vulnerability detection, patch approval, staged deployment, and compliance verification cycle, executed without administrator intervention for patches that meet predefined risk criteria.
The zero-touch patching pipeline in an AEM platform operates through several automated stages:
Stage 1: Continuous vulnerability detection. The agent monitors installed software versions against a continuously updated CVE database. When a new vulnerability is published that affects installed software on any managed device, the affected devices are identified within hours, not days.
Stage 2: Risk-based auto-approval. Patch approval policies define the conditions under which patches are automatically approved without human review. Critical severity CVEs (CVSS 9.0 and above with known active exploits) are auto-approved immediately. High severity patches auto-approve after a 24-hour window. Medium and low severity patches route through a manual approval queue. This logic ensures that the patches requiring fastest response receive it automatically, while lower-priority patches maintain human oversight.
Stage 3: Staged ring deployment. Auto-approved patches deploy through pre-configured rings: test devices first (immediate), pilot group second (24 to 48 hours after test success), production broad ring third (5 to 7 days after pilot validation). Deployment failures in any ring halt progression and generate alerts. This staged approach applies the discipline of controlled rollout to patches that cannot wait for manual scheduling.
Stage 4: Third-party application patching. OS patches are only part of the vulnerability surface. Browsers, PDF readers, communication tools, developer frameworks, and runtime libraries all carry patchable CVEs. Zero-touch patching in AEM covers third-party applications on the same automated pipeline as OS updates, closing the gap that WSUS and native update tools leave open.
Stage 5: Automated compliance verification and reporting. After each patch ring completes, the platform automatically generates compliance reports showing patch success rates, failure analysis, and updated fleet MTTP. These reports are available immediately for audit purposes without manual evidence collection.
NIST SP 800-40 Rev. 4 defines critical CVE remediation within 72 hours to 7 days as the enterprise standard. Zero-touch patching is the only mechanism that makes this standard operationally achievable at scale. Explore Zecurit's patch management and what is patch management for a deeper look at the technical implementation.
Autonomous deployment shifts software delivery from an administrator-initiated task to an intent-driven automated process. The administrator defines the intent: "All devices in the Engineering group must have the latest version of the security agent, the approved browser, and the VPN client." From that point, the platform enforces the intent continuously, including for new devices that join the group.
This "targeted intent" model has a specific operational impact on onboarding. In a traditional UEM environment, a new device enrolling in the platform requires an administrator to identify it, assign it to the correct group, and initiate software deployment. In an AEM environment, the enrollment triggers automated group assignment based on device attributes (user role, department, OS version, location), which automatically triggers the software deployment policies assigned to that group. The device is fully provisioned to its defined configuration without any administrator action beyond the initial policy setup.
Autonomous deployment also maintains software state continuously after initial provisioning. If a required application is uninstalled by a user or removed during a system event, the platform detects the missing software and reinstalls it automatically without waiting for an administrator to notice and act.
Zecurit's software deployment supports this intent-based model for Windows, macOS, and Linux environments. Related capabilities include zero-touch software deployment, silent software installation, and bulk software deployment.
Self-healing is the AEM capability that most directly reduces MTTR for operational incidents. It combines continuous monitoring with automated script execution to detect common failure conditions and resolve them within minutes, before users experience the impact or before a helpdesk ticket is ever raised.
Self-healing in practice operates through alert-triggered script execution: a monitoring condition fires an alert, which automatically triggers a predefined remediation script, which resolves the condition, which clears the alert, which generates an event log entry. No human in the loop. No ticket. No delay.
AEM If/Then Logic: Self-Healing Automation in Practice
| IF (Detected Condition) | THEN (Autonomous Action) | Outcome |
|---|---|---|
| BitLocker encryption is disabled on a managed device | Re-enable BitLocker via configuration policy, escrow recovery key, log compliance event | Device returns to encrypted state within minutes; audit trail generated |
| Disk usage exceeds 85% on any endpoint | Execute cleanup script: clear temp files, Windows Update cache, user download folders (>30 days) | Disk usage drops below threshold; alert resolves; no helpdesk ticket raised |
| Security agent (EDR/AV) service stops running | Restart the service via watchdog script; send alert if restart fails after 3 attempts | Service restored within seconds; failure escalated only if auto-remediation fails |
| OS patch level falls >30 days behind release | Trigger patch deployment workflow; apply ring assignment; initiate deployment window | Device patched to compliance; MTTP metric updated; report refreshed |
| Configuration drift detected (firewall/SSH changes) | Reapply the baseline configuration profile to the affected setting; log the drift event | Configuration restored to baseline; drift event recorded for security review |
| New device enrolls without required software | Detect missing software against group policy; trigger silent installation of all required apps | Device fully provisioned to defined standard without administrator action |
| User account created with unauthorized local admin rights | Detect elevated privilege assignment; remove admin rights; notify security team | Privilege escalation contained automatically; security team informed for follow-up |
Zecurit's remote script execution is the engine powering self-healing workflows. Scripts are stored in a centralized repository, can be triggered by alert conditions automatically, and execute across the fleet simultaneously with real-time output capture and per-device status tracking. The remote script deployment guide provides implementation detail for building self-healing automation pipelines.
Adaptive security is the AEM pillar that integrates security posture assessment into management decisions in real time. Rather than applying the same static policy to every device regardless of its current risk state, adaptive security shifts policy enforcement dynamically based on what the platform knows about each device's current condition.
The practical implementation of adaptive security works through device risk scoring. Every managed device carries a continuously updated risk score derived from its current patch level, security agent health, configuration compliance, user activity patterns, and any active security alerts. As the risk score changes, the enforcement policies applied to the device adjust accordingly.
A device in good standing (fully patched, compliant configuration, healthy security agent, no active alerts) operates under standard access policies. A device that falls out of compliance (missed a critical patch, security agent stale, firewall rule changed) automatically receives a more restrictive policy set: reduced network access, additional monitoring, priority remediation queue placement, and notification to the security team.
This dynamic enforcement model is the operationalization of Zero Trust Architecture principles at the device level. Compliance is not assumed; it is verified continuously. Access is not granted permanently; it is conditional on maintained compliance. Zecurit's endpoint monitoring and alerts and configuration management provide the continuous visibility and policy enforcement layer that makes adaptive security operationally real rather than theoretically aspirational.
For organizations subject to regulatory frameworks such as SOC 2, HIPAA, PCI-DSS, ISO 27001, or CMMC, autonomous endpoint management provides a compliance dividend that goes beyond operational efficiency. It transforms compliance from a periodic audit exercise into a continuous operational state.
The compliance requirements that AEM addresses directly include:
Zecurit's reports and auditing module produces pre-built compliance reports mapped to these frameworks, generated automatically on schedule or on demand.
Understanding where your organization sits on the autonomy curve is the starting point for building an AEM roadmap. Use this maturity assessment to evaluate your current state across the five pillars.
Inventory Maturity
Patch Management Maturity
Deployment Maturity
Self-Healing Maturity
Security Posture Maturity
Most organizations land at Level 2 across most pillars. Moving to Level 3 across all five pillars is the practical definition of achieving Autonomous Endpoint Management.
Most IT teams are operating at Stage 2 on the autonomy curve. Zecurit gives you the platform to reach Stage 3: real-time continuous inventory, zero-touch patch automation, intent-based software deployment, self-healing script workflows, and adaptive security enforcement across your entire fleet.
Start with the capabilities that deliver the fastest ROI:
Explore the full Zecurit feature set or see how the platform covers your complete cross-platform environment including Windows endpoint management.
• No credit card required • 14 day free trial
No, and framing AEM as a headcount reduction technology misunderstands what it does. AEM replaces repetitive, low-judgment tasks: applying a patch, restarting a service, clearing disk space, re-enabling a firewall rule. These tasks consume significant engineering time but require no strategic thinking. When a platform handles them autonomously, the engineers who were doing them are freed to do work that actually requires their expertise: designing architecture, evaluating new technologies, building automation frameworks, and improving security posture. Every organization that has successfully implemented IT hyper-automation has found that it changes what their IT team does, not whether they need one. The Gartner research on hyper-automation in IT operations consistently finds that automation increases the strategic value of IT teams rather than replacing them.
Control in an AEM system is exercised at the policy layer rather than the execution layer. You define the rules; the platform enforces them. Every autonomous action is bounded by the policies you configure: which patch severities auto-approve, which remediation scripts run automatically, which conditions trigger escalation to a human, and which actions always require manual approval. You can make the system as autonomous or as human-supervised as your risk tolerance requires, and adjust that calibration over time as confidence in the automation grows. Every autonomous action is logged with full detail: what triggered it, what action was taken, on which device, at what time, and what the outcome was. You have complete visibility into everything the platform does on your behalf, and you retain the ability to override, pause, or modify any autonomous workflow at any time through Zecurit's configuration management and policy controls.
Yes, and in many respects AEM produces a stronger compliance posture for regulated industries than manual management does. The fundamental compliance challenge in regulated environments is not that the right controls are undefined; it is that controls drift between audit cycles because manual enforcement cannot keep pace with the rate of change across a device fleet. AEM solves this by enforcing controls continuously rather than periodically. A HIPAA-regulated organization using AEM has BitLocker enforced on every device at all times, not just when an auditor checks. Patch compliance is maintained within the required remediation window continuously, not restored before an audit. Audit evidence is generated automatically, not assembled manually. The result is a compliance posture that is genuinely maintained rather than demonstrated at audit time. See Zecurit's endpoint security guidance and Zero Trust implementation guide for the security architecture underpinning these controls.
RMM (Remote Monitoring and Management) is a tool category focused on remote access, alerting, and scripted automation, primarily designed for MSPs managing client environments. AEM is an operating philosophy that uses RMM-like capabilities (monitoring, scripting, remote access) combined with UEM-like capabilities (policy enforcement, compliance, lifecycle management) to achieve autonomous operations. The difference is in the design goal: RMM gives a technician tools to respond; AEM gives the platform the authority to respond. Zecurit's what is RMM guide covers the distinction in more detail.
AEM applies to any endpoint type that can run a management agent or be reached through an API: Windows workstations and servers, macOS devices, Linux endpoints and servers, mobile devices through MDM enrollment, and network-connected IoT and infrastructure devices through agentless discovery. The core AEM principles (continuous inventory, zero-touch patching, autonomous deployment, self-healing, adaptive security) apply across all of these device types, though the specific implementation mechanisms vary by platform. See what is unified endpoint management for the cross-platform management foundation that AEM builds on.