SCCM vs. Modern UEM: The 2026 Migration Guide
Complete guide to migrating from SCCM to modern UEM in 2026. Compare costs, capabilities & implementation strategies for cloud-native endpoint management

Moving from reactive, calendar-driven patching to a proactive, autonomous, and risk-intelligent vulnerability management program is not a technology problem. It is an architectural and cultural transformation. Here is the distilled guidance for SecOps teams, Compliance Officers, and MSPs entering the second half of 2026:
1. Kill the monthly cycle. EPSS-tiered SLAs replace Patch Tuesday as your operational cadence. Critical vulnerabilities with high exploitation probability demand sub-24-hour response. Anything less is an acceptable risk acceptance decision, not a default behavior.
2. Automate the testing pipeline. Human review of every patch is no longer scalable. AI-driven digital twin testing and automated rollback triggers maintain deployment safety without sacrificing speed.
3. Integrate patching with access control. Patch compliance should be a first-class zero-trust posture signal. Non-compliant endpoints lose privileged access automatically, immediately, and reversibly upon remediation.
4. Expand your scope. Patch management in 2026 covers IoT firmware, third-party applications, driver updates, PQC cryptographic libraries, and compensating controls for patch-less vulnerabilities. If it touches your network, it belongs in your vulnerability management pipeline.
5. Close the loop with attestation. Deployment confirmation is not the same as vulnerability closure. Cryptographic attestation from the endpoint's TPM is the only evidence-grade verification that satisfies modern compliance requirements.
6. Treat vulnerability management and patch management as one discipline. The organizations that will win against 2026-era adversaries are those who have dissolved the artificial silos between these functions and built a unified, continuous remediation pipeline.
In 2026, the phrase "we'll patch it on Patch Tuesday" has become the IT equivalent of leaving your front door open and hoping no one notices.
The threat landscape has undergone a seismic shift. Autonomous AI exploit frameworks, operating with machine-speed precision, can analyze a freshly disclosed CVE, synthesize a working proof-of-concept, and begin scanning the public internet for vulnerable hosts in under eleven minutes of the NVD publication timestamp. The days of a comfortable 30-day remediation window are over. In many cases, organizations that wait even 72 hours are already responding to incidents rather than preventing them.
This is the new reality that has given rise to what analysts are calling "Patching Fatigue": a dangerous exhaustion born not from too little patching activity, but from too much of the wrong kind. Security teams are drowning in a flood of CVE notifications, vendor advisories, and compliance mandates. The average enterprise endpoint manager now receives more than 900 patch notifications per month across operating systems, third-party applications, firmware, and drivers. When everything is urgent, nothing is prioritized, and threat actors exploit exactly that paralysis.
The traditional Patch Tuesday cadence, which was Microsoft's monthly release cycle that the broader industry followed for two decades, was designed for a world where exploit development took weeks and network perimeters were clearly defined. That world no longer exists. Today's hybrid work environments, cloud-native workloads, containerized applications, and sprawling IoT ecosystems mean that endpoint security is a continuous discipline, not a monthly checkbox.
This article presents the definitive 2026 framework for modern patch management: one grounded in risk-based intelligence, autonomous patching pipelines, zero-trust integration, and post-quantum cryptographic readiness. Whether you are a SecOps engineer, a Compliance Officer under NIS2 or HIPAA mandates, or an MSP managing hundreds of client environments, this guide will help you architect a vulnerability management program that closes the gap between disclosure and remediation, before adversaries exploit it.
Before examining best practices, it is worth internalizing the mathematical reality of modern exploitation.
The probability of exploitation for an unpatched vulnerability can be modeled using an exponential distribution function based on the time elapsed since public disclosure:
P(E)=1−e−λt
Where:
For a high-severity vulnerability with an EPSS score above 0.7 (indicating a 70%+ probability of exploitation in the wild within 30 days), the value of λ\lambda λ can be as high as 0.15 to 0.25. This means that for a critical unpatched system, P(E)P(E) P(E) exceeds 0.50 (50% likelihood of an active exploit attempt) within just four to five days of disclosure.
This model underscores why vulnerability management can no longer be a periodic activity. It must be a continuous, risk-calibrated, data-driven process.
| Dimension | Legacy Patch Management | Modern Autonomous Vulnerability Management |
|---|---|---|
| Cadence | Monthly (Patch Tuesday) | Continuous, real-time |
| Prioritization Method | CVSS score only | EPSS + asset criticality + exploit telemetry |
| Testing Approach | Manual staging environment | AI-driven digital twins and isolated containers |
| Deployment Model | Push to all endpoints simultaneously | Phased ring-based rollout with auto-rollback |
| Rollback Capability | Manual, slow, high-risk | Automated trigger-based rollback in minutes |
| Scope | OS and major applications | OS, applications, firmware, drivers, IoT, OT |
| Remote/Hybrid Coverage | VPN-dependent, bandwidth-constrained | Cloud-native agent with delta patching |
| Compliance Verification | Periodic scan-based attestation | Continuous automated attestation per endpoint |
| Zero-Trust Integration | None | Automatic quarantine for non-compliant endpoints |
| Patch-Less Vulnerabilities | Not addressed | Covered via virtual patching and compensating controls |
| PQC/Firmware Readiness | Ignored | Mandatory track in remediation pipeline |
| Tool Footprint | Siloed patch tool + separate vuln scanner | Unified endpoint management platform |
The foundational error of legacy patch management is the instinct to treat every CVE equally. In a world where enterprise environments may expose hundreds of vulnerabilities per week, treating a CVSS 4.2 informational finding with the same urgency as an actively exploited remote code execution vulnerability is not just inefficient. It is operationally dangerous because it dilutes the focus of your SecOps team.
The 2026 standard for prioritization centers on three integrated signals:
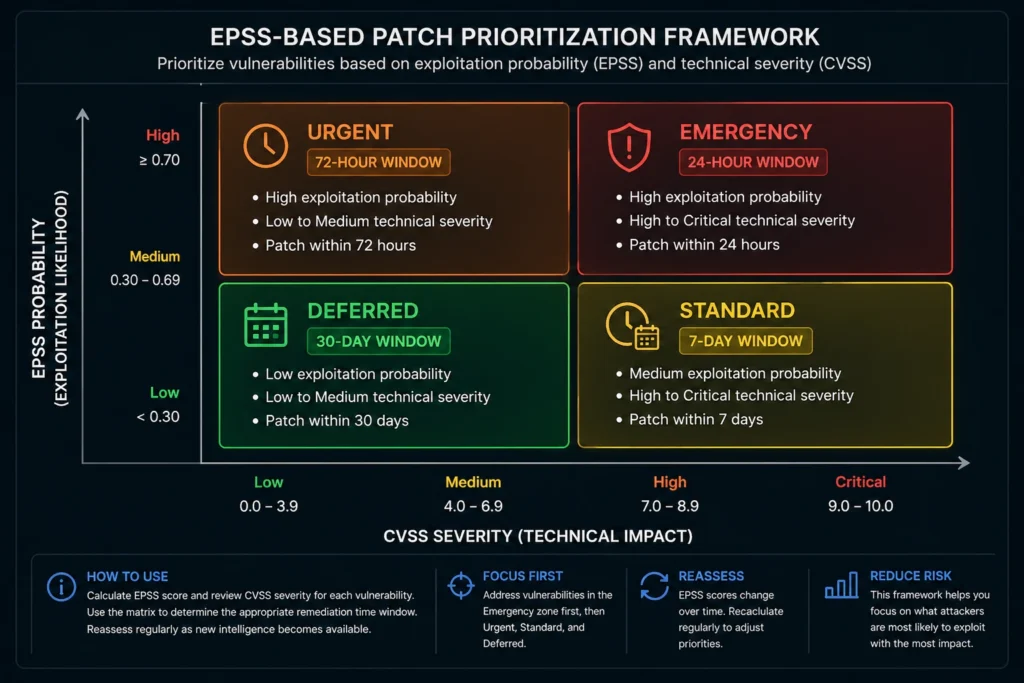
The Exploit Prediction Scoring System (EPSS). Developed by FIRST (Forum of Incident Response and Security Teams) and now in its third major iteration, EPSS provides a machine-learning-derived probability score (0.0 to 1.0) representing how likely a given CVE is to be exploited in the wild within the next 30 days. Unlike CVSS, which measures theoretical severity, EPSS measures observed threat intelligence. SecOps teams should define dynamic patching SLAs based on EPSS thresholds:
Asset Criticality Weighting. Not all endpoints are equal. A domain controller, a patient records server, or a payment processing terminal carries exponentially more business risk than a standard employee workstation. Your prioritization framework must incorporate a CMDB or IT asset management system that classifies assets by their blast radius, regulatory scope (PCI-DSS, HIPAA, NIS2), and network segment sensitivity. Multiply the EPSS-derived urgency score by the asset criticality weight to produce a final remediation priority score.
Threat Intelligence Enrichment. Integrate your patching pipeline with threat intelligence feeds (CISA KEV catalog, vendor bulletins, commercial CTI providers) to detect when vulnerabilities transition from theoretical to actively weaponized. A CVE with a modest EPSS of 0.3 that appears in a CISA KEV update should immediately be escalated to emergency patching status regardless of its static score.
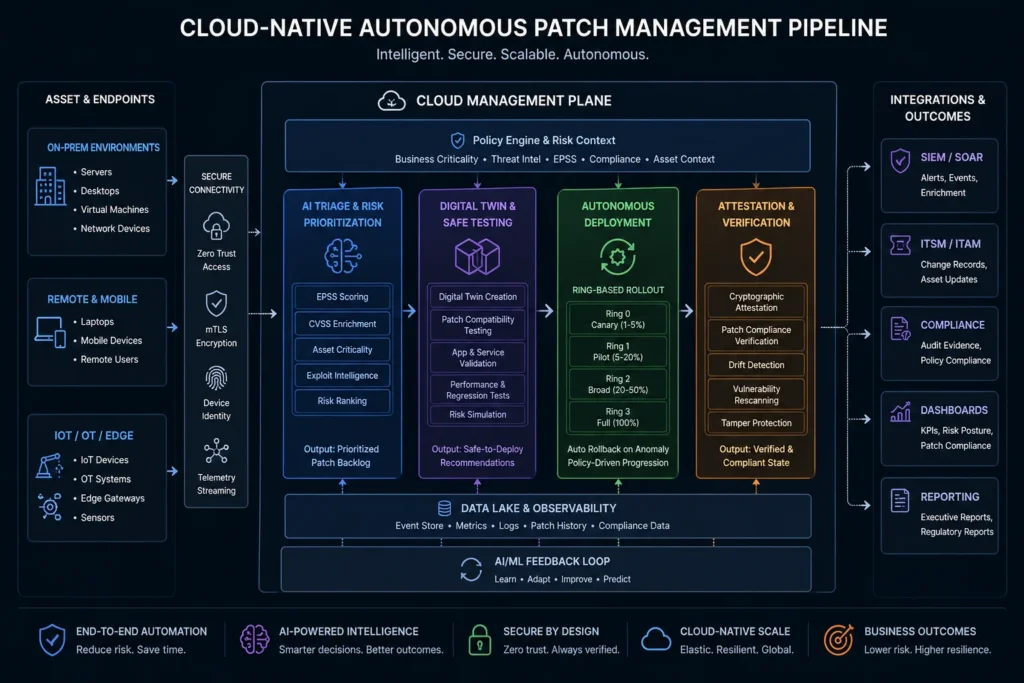
The volume and velocity of vulnerability disclosures in 2026 have made purely human-driven patch management pipelines untenable at scale. Organizations managing more than 500 endpoints cannot realistically test, approve, and deploy patches manually without accumulating dangerous backlogs. The answer is an autonomous endpoint management architecture powered by AIOps.
A mature autonomous patching pipeline consists of three integrated layers:
Layer 1: Intelligent Ingestion and Triage. AI agents continuously monitor NVD, vendor security bulletins, CISA KEV, and proprietary threat intelligence streams. Upon detecting a new CVE relevant to your asset inventory, the agent automatically retrieves the patch package, validates its cryptographic signature against the vendor's published hash, and cross-references the affected asset list against your hardware inventory and software inventory. This entire triage cycle should complete in under five minutes.
Layer 2: Containerized Pre-Production Testing. Before any patch touches a production endpoint, it must pass through an automated validation pipeline. In 2026, best-practice organizations use digital twin environments, which are lightweight and ephemeral virtual replicas of production system configurations, to simulate patch installation, test for compatibility conflicts, validate application stack behavior post-patch, and run automated regression test suites. This is the direct evolution of the traditional staging server concept, but at machine speed and cloud scale. Container-based testing can complete a full validation cycle in 15 to 45 minutes for most standard patches. For complex firmware or kernel updates, allow up to four hours for comprehensive simulation before greenlighting production deployment.
Key AI behaviors in this layer include: automatic rollback trigger generation (defining specific error conditions that will immediately revert the patch), dependency chain analysis, and service restart sequencing to minimize user-facing downtime.
Layer 3: Phased Deployment with Telemetry-Gated Rollout. Even after successful pre-production testing, patches should deploy through a ring-based architecture. Ring 0 (canary group: 1-2% of endpoints, typically IT team devices) deploys first. Telemetry from Ring 0 is analyzed over a defined observation window (typically 4-8 hours for non-critical patches, 1-2 hours for emergency patches). If anomaly rates remain below defined thresholds, the pipeline automatically promotes the patch to Ring 1 (10% of fleet), then Ring 2 (40%), and finally Ring 3 (remaining endpoints). See the deployment scheduling guide for implementation specifics.
Expert Insight
Zero-trust security operates on the principle that no device, user, or workload should be inherently trusted. Access must be continuously verified against a set of real-time posture signals. In 2026, patch compliance status has become one of the most critical posture signals in any zero-trust architecture.
The integration point is straightforward but powerful: if an endpoint fails to apply a critical or high-severity patch within its defined SLA window, it should automatically trigger a policy-driven response at the network access layer. Depending on the severity and the asset classification, the response may range from restricted network access (blocking access to sensitive segments while allowing internet and productivity tools) to full quarantine (redirecting all traffic to a captive remediation portal).
This automated enforcement model, often called "patch-gated access," creates a powerful behavioral incentive for endpoint compliance. It also provides compliance officers with a defensible, audit-ready record of when non-compliant endpoints were isolated, what remediation was applied, and when full access was restored.
Implement patch-gated zero-trust enforcement in four steps:
For remote and hybrid workers, this model is particularly valuable. Cloud-native agents that communicate over HTTPS on port 443 ensure that patch compliance is enforced regardless of whether the endpoint is on the corporate LAN, a home broadband connection, or a coffee shop WiFi.
While much of the patch management conversation in 2026 centers on application and OS vulnerabilities, there is a parallel and critically urgent remediation track that many organizations are still neglecting: the transition to Post-Quantum Cryptography (PQC) compliant algorithms.
NIST finalized its first suite of PQC standards (FIPS 203, 204, and 205) in 2024, and the zero-day vulnerability clock on harvest-now-decrypt-later attacks began ticking immediately. Nation-state threat actors with access to early-stage quantum computing resources are actively harvesting encrypted traffic today with the intent to decrypt it once cryptographically relevant quantum computers become available.
Your 2026 patch management pipeline must include a dedicated PQC firmware and software remediation track:
Firmware patching for cryptographic agility. Ensure that network devices, HSMs (Hardware Security Modules), VPN concentrators, and TPM (Trusted Platform Module) chips receive firmware updates that introduce support for ML-KEM (CRYSTALS-Kyber, FIPS 203) for key encapsulation and ML-DSA (CRYSTALS-Dilithium, FIPS 204) for digital signatures. Many enterprise hardware vendors began shipping PQC-capable firmware in 2025-2026; your IT asset tracking system should maintain a record of firmware versions and flag devices that have not yet received PQC-capable updates.
TLS 1.3 enforcement and hybrid PQC deployment. Patch and configure web servers, load balancers, and API gateways to support hybrid key exchange mechanisms that combine classical ECDH with ML-KEM, providing protection against both classical and quantum adversaries during the transition period.
Certificate lifecycle management. Begin inventorying all certificates signed with RSA-2048 or ECDSA P-256, and establish a migration plan to migrate to PQC-compliant certificates issued under ML-DSA before the end of 2026.
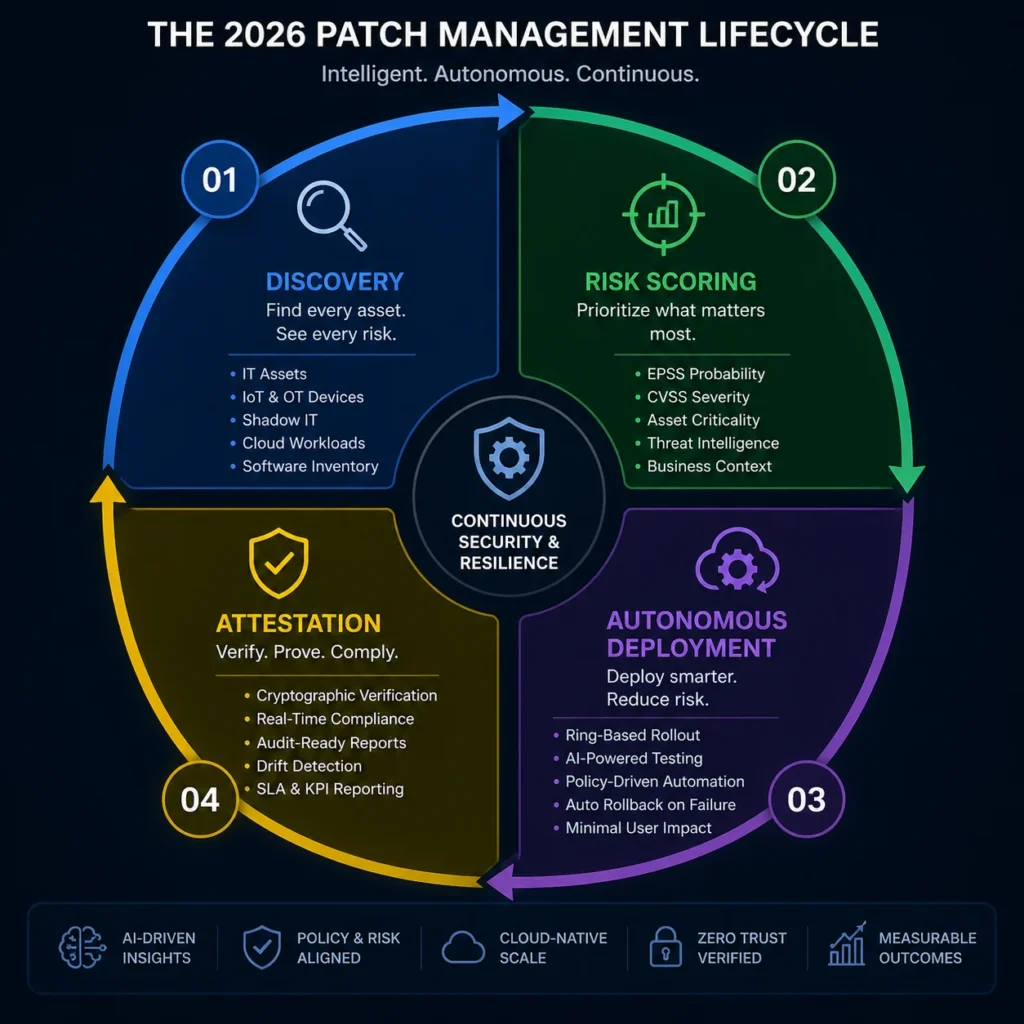
A high-performance vulnerability management program in 2026 follows a continuous four-phase lifecycle. Unlike the traditional waterfall-style "scan, report, remediate" model, the 2026 lifecycle is a closed-loop, automated system where each phase feeds intelligence back into the preceding ones.
You cannot patch what you do not know exists. In 2026, the scope of "what exists" has expanded dramatically to encompass:
Effective discovery in 2026 requires a multi-method approach. Authenticated agent-based scanning provides the deepest software inventory on managed endpoints. Agentless network scanning using SNMP, WMI, SSH, and API integrations covers infrastructure and semi-managed assets. Passive network traffic analysis using NDR (Network Detection and Response) sensors discovers shadow IT and unmanaged IoT devices by fingerprinting their network behavior without requiring any installed agent.
The output of this discovery layer must feed directly into a hardware inventory and software inventory database that updates in near-real time. Static monthly inventory scans are no longer acceptable. Every new device enrollment, software installation, or configuration change should trigger an immediate inventory delta update. This is the foundation upon which all downstream risk prioritization and patch targeting is built.
For MSPs managing multi-tenant environments, the IT asset discovery tools and IT inventory management capabilities must provide full tenant isolation while enabling cross-tenant reporting for benchmarking and compliance purposes.
The single most common cause of patch-induced outages is insufficient pre-deployment testing. Yet traditional staging environments are too slow, too expensive to maintain at scale, and too dissimilar from production configurations to catch all compatibility issues.
Digital twin testing addresses this by creating ephemeral, high-fidelity virtual replicas of production endpoints on demand. Each digital twin is initialized from the latest configuration snapshot of a representative endpoint in the target ring. The AI testing agent then executes a standardized validation protocol:
The testing agent generates a structured validation report with a Go/No-Go recommendation and a confidence score. For Go decisions, it also generates the rollback trigger conditions that will be used during production deployment. These conditions typically include specific error codes, service failure patterns, or performance degradation thresholds that, if observed on any Ring 0 device during deployment, will immediately halt further rollout and initiate automated rollback.
Deployment in 2026 is not a binary "push to all" operation. It is a choreographed, telemetry-gated, ring-based progression as described in the AIOps section above. A few additional deployment considerations are worth highlighting for 2026:
Bandwidth-Aware Deployment Scheduling. For remote endpoints on limited bandwidth connections (branch offices, field workers on LTE/5G), patches should use delta-compression techniques that transmit only the changed binary blocks rather than entire package files. This can reduce patch payload sizes by 60-85% for incremental updates. Additionally, deployment scheduling policies should be configured to enforce patching during off-peak hours (typically overnight or weekends) to avoid saturating user connections during business hours.
Patch-Less Vulnerability Mitigation. Not every vulnerability can be remediated by a traditional patch. Vendor-provided workarounds, configuration changes, virtual patching via WAF rules, or temporary service disablement are sometimes the only available remediation for zero-days or end-of-support components. These compensating controls must be tracked in the same vulnerability management pipeline as traditional patches, with explicit expiry dates that trigger re-evaluation when a traditional patch becomes available. Your configuration management capabilities play a critical role here, enabling the automated deployment of configuration-based compensating controls at scale.
Third-Party Application Patching. Microsoft OS patches represent only a fraction of enterprise remediation workload. Third-party applications (browsers, PDF readers, productivity suites, developer tools) often represent the highest-exploitation-frequency attack surface. Ensure your patch management platform supports automated third-party software deployment and not merely OS-level patching.
Deploying a patch is necessary but not sufficient. Many organizations have experienced scenarios where a patch was technically deployed but failed to install correctly due to a conflict, an incomplete restart, or a corrupted package, leaving the vulnerability technically open while appearing closed in the dashboard.
Verification in 2026 must go beyond "deployment status: success." It requires cryptographic attestation: a process where the endpoint agent independently verifies the vulnerability closure by checking:
The attestation record should be signed by the endpoint's TPM module, creating a tamper-evident audit trail that satisfies compliance requirements for NIST SP 800-53, ISO 27001, NIS2, HIPAA, and PCI-DSS. This attestation data feeds directly into your reports and auditing workflows, enabling compliance officers to generate evidence-grade remediation reports without manual data collection.
Not every security gap has a vendor patch. In 2026, several categories of "unresolvable" or "delayed-resolution" vulnerabilities require special handling:
Zero-day vulnerabilities: Between disclosure and vendor patch availability, organizations must rely on virtual patching (WAF rules, IPS signatures), configuration hardening (disabling the vulnerable feature or protocol), and network segmentation to reduce blast radius.
End-of-support components: Windows 10 reached end of life in 2025, and many organizations still carry a tail of EoL operating systems and applications. These components will never receive another security update. The risk management approach for EoL components must combine aggressive application allowlisting, compensating network controls, accelerated hardware refresh planning, and explicit risk acceptance documented at the CISO level.
Supply chain vulnerabilities: Compromises embedded in software build pipelines (a recurring threat vector since SolarWinds) may not manifest as traditional CVEs at all. Integrate software composition analysis (SCA) and software bill of materials (SBOM) validation into your patch ingestion pipeline. For more context, see the supply chain attack guide.
The dispersed workforce of 2026 presents a unique operational challenge: how do you maintain patch compliance for endpoints that may spend most of their operational life off the corporate network, connected via variable-quality consumer internet connections?
The answer requires three architectural decisions:
Cloud-native agent architecture. Your endpoint management agent must communicate via HTTPS on port 443 to a cloud management plane, requiring no VPN and no on-premises infrastructure dependency. Agents should use persistent connections with exponential backoff reconnect logic to handle intermittent connectivity without losing compliance status.
Delta and differential patching. As noted above, delivering only the changed binary blocks (rather than full replacement packages) is essential for remote endpoint management. This is standard practice for OS updates (Microsoft's binary delta compression, Apple's chunked updates) but must also be enforced for third-party application updates.
Peer-to-peer distribution (P2P caching). For environments with multiple remote users in the same geographic location (remote offices, home users in the same region), configure your patch distribution infrastructure to use P2P caching so that once one device in a location downloads a patch, neighboring devices can source it locally rather than pulling from a central server. This is particularly valuable for large firmware updates or feature-level OS upgrades that can be several gigabytes in size.
A unified endpoint management platform should serve as the operational hub for your patching program, consolidating the following capabilities under a single pane of glass:
For MSPs, the platform must add multi-tenant management, per-client SLA enforcement, and white-labeled compliance reporting. The best patch management software comparison guide provides a detailed evaluation matrix for platform selection.
When evaluating platforms, prioritize the following 2026-specific criteria: native EPSS integration, support for third-party application patching, digital twin or containerized pre-production testing capabilities, cloud-native agent architecture for remote endpoints, and built-in PQC firmware update support.
For a broader view of how patch management fits into your overall endpoint security posture, see the what is endpoint security and vulnerability scanning guides.
| Regulatory Framework | Relevant Requirement | Framework Alignment |
|---|---|---|
| NIST SP 800-53 Rev 6 | SI-2 (Flaw Remediation), CM-6 (Configuration Settings) | EPSS-tiered SLAs + cryptographic attestation |
| NIS2 Directive (EU) | Article 21 - Vulnerability handling, patch management | Continuous discovery + 24/72-hour remediation SLAs |
| PCI-DSS v4.0 | Requirement 6.3 (Security vulnerabilities addressed) | Automated patch deployment + attestation reports |
| HIPAA Security Rule | 164.308(a)(5) - Security awareness and training / patch mgmt | Risk-based prioritization for ePHI systems |
| CIS Controls v8.1 | Control 7 (Continuous Vulnerability Management) | Full lifecycle coverage: discovery through verification |
| ISO/IEC 27001:2022 | A.8.8 - Management of technical vulnerabilities | Unified vulnerability management pipeline |
For a deeper look at building a security audit trail that satisfies these frameworks, see the how to perform a security audit guide. For HIPAA-specific endpoint compliance considerations, the HIPAA compliance guide provides additional context.
For further reading on implementing these practices with Zecurit's unified endpoint management platform, explore the autonomous endpoint management capabilities, the zero-trust security implementation guide, and the full endpoint management features overview.
Zecurit Endpoint Manager gives your team real-time vulnerability intelligence, automated patch deployment, and zero-trust compliance enforcement, all from one unified platform. See it in action today.
Complete guide to migrating from SCCM to modern UEM in 2026. Compare costs, capabilities & implementation strategies for cloud-native endpoint management

Discover how IT Directors eliminate software sprawl with proven frameworks. Reduce SaaS waste, improve security, and recover millions in hidden costs. Complete strategic guide.
Learn how to cut Adobe Creative Cloud costs 20-30% with strategic license management.